linux iptables security technology and firewall
Linux's iptables is a widely used firewall tool that can be used to monitor and control network traffic to ensure network security. It has powerful features and configuration options to customize rules as needed to protect against malicious attacks and unknown access. iptables effectively protects servers from network threats by filtering and forwarding data packets. Its flexibility and reliability make it the tool of choice for many system administrators and network engineers to maintain and manage network security. The role of iptables is not only to prevent intrusions, but also to
The following are some key points of iptables security technology and firewall:
- Firewall rules: iptables allows administrators to create and configure firewall rules to control the incoming and outgoing network traffic. Rules can be defined based on source IP address, destination IP address, port number, protocol, etc. Administrators can define whether to allow or deny specific traffic, and set up more complex rules as needed.
- Network Address Translation (NAT): iptables supports the network address translation function, which can realize the conversion of IP addresses and ports. This is useful for hiding the real IP address of an internal network or implementing port forwarding.
- Prevent Denial of Service (DoS) attacks: iptables can configure rules to limit the number of connections from a single IP address or range of IP addresses. This helps prevent denial of service attacks and limit resource consumption of the server by malicious users.
- Status tracking: iptables can track the status of the connection and process it based on the status of the connection. It can identify new connections, established connections, related connections and invalid connections and perform appropriate actions as needed.
- Packet filtering and firewall chains: iptables organizes rules through firewall chains and can filter according to different stages of traffic. Common firewall chains include INPUT (receive packets), OUTPUT (send packets), and FORWARD (forward packets).
- Logging: iptables can configure rules to record packet information that matches specific rules, including source IP address, destination IP address, port, etc. This is useful for auditing and troubleshooting.
- Other functions: iptables also provides other functions, such as connection tracking, network address translation (NAT), port forwarding, user-defined chains, etc. These features make iptables a powerful and flexible tool suitable for a variety of network security needs.
In general, iptables is a powerful firewall tool that can effectively improve the security of Linux servers through flexible configuration of rules and functions. Administrators can use iptables to manage and protect network traffic, prevent unauthorized access, and monitor and respond to malicious behavior. iptables has a rich set of features and options to customize firewall policies as needed, including allowing or denying traffic to specific IP addresses, ports, or protocols. In addition, iptables also supports the Network Address Translation (NAT) function, allowing administrators to configure port forwarding and address translation to achieve secure communication between the server and the external network. By properly configuring iptables rules, administrators can effectively reduce the security risks faced by the server and ensure that the system runs in a relatively stable environment.
Please note that the usage and configuration options of iptables may vary between different Linux distributions and versions. Administrators will need to consult relevant documentation and resources to learn about best practices and configuration methods for their specific environment. iptables is a powerful tool that can help administrators control and manage network traffic and enhance system security. Therefore, proficiency in the configuration and use of iptables is crucial to ensuring the stability and security of the system. Administrators should regularly update their knowledge to keep up with the latest developments and best practices in iptables. Through in-depth study and practice, administrators canThe above is the detailed content of linux iptables security technology and firewall. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Win11 firewall advanced settings gray solution
Dec 24, 2023 pm 07:53 PM
Win11 firewall advanced settings gray solution
Dec 24, 2023 pm 07:53 PM
When setting up the firewall, many friends found that their win11 firewall advanced settings were grayed out and unable to be clicked. This may be caused by not adding a control unit, or by not opening the advanced settings in the correct way. Let’s take a look at how to solve it. Win11 firewall advanced settings gray method one: 1. First, click the start menu below, search and open "Control Panel" at the top 2. Then open "Windows Defender Firewall" 3. After entering, you can open "Advanced Settings" in the left column . Method 2: 1. If the above method cannot be opened, you can right-click "Start Menu" and open "Run" 2. Then enter "mmc" and press Enter to confirm opening. 3. After opening, click on the upper left
 How to enable or disable firewall on Alpine Linux?
Feb 21, 2024 pm 12:45 PM
How to enable or disable firewall on Alpine Linux?
Feb 21, 2024 pm 12:45 PM
On AlpineLinux, you can use the iptables tool to configure and manage firewall rules. Here are the basic steps to enable or disable the firewall on AlpineLinux: Check the firewall status: sudoiptables -L If the output shows rules (for example, there are some INPUT, OUTPUT, or FORWARD rules), the firewall is enabled. If the output is empty, the firewall is currently disabled. Enable firewall: sudoiptables-PINPUTACCEPTsudoiptables-POUTPUTACCEPTsudoiptables-PFORWARDAC
 How to remove the firewall logo on the Win10 desktop icon?
Jan 01, 2024 pm 12:21 PM
How to remove the firewall logo on the Win10 desktop icon?
Jan 01, 2024 pm 12:21 PM
Many friends who use win10 system find that there is a firewall logo on the icon on the computer desktop. What is going on? This makes many friends with obsessive-compulsive disorder particularly uncomfortable. In fact, we only need to open the control panel and click " It can be solved by changing "Change User Account Control Settings". Let's take a look at the specific tutorial. How to cancel the firewall logo on the desktop icon in Windows 10 1. First, right-click the Start menu button next to the computer startup screen, and then select the Control Panel function from the pop-up menu. 2. Then select the "User Account" option and select the "Change User Account Control Settings" item from the new interface that appears. 3. After adjusting the slider in the window to the bottom, click Confirm to exit.
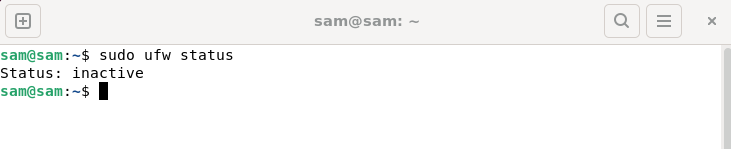 How to fix UFW status showing as inactive in Linux
Mar 20, 2024 pm 01:50 PM
How to fix UFW status showing as inactive in Linux
Mar 20, 2024 pm 01:50 PM
UFW, also known as Uncomplex Firewall, is adopted by many Linux distributions as their firewall system. UFW is designed to make it easy for novice users to manage firewall settings through both the command line interface and the graphical user interface. A UFW firewall is a system that monitors network traffic according to set rules to protect the network from network sniffing and other attacks. If you have UFW installed on your Linux system but its status shows as inactive, there could be several reasons. In this guide, I will share how to resolve the UFW firewall inactive issue on Linux systems. Why UFW Shows Inactive Status on Linux Why UFW Is Inactive by Default on Linux How to Inactive on Linux
 Local IP address query
Jan 05, 2024 pm 01:42 PM
Local IP address query
Jan 05, 2024 pm 01:42 PM
The methods for querying the IP address of this machine are: 1. Under Windows system, open the "Start Menu" and search for "cmd" to open the command prompt, enter "ipconfig", and then press the Enter key to find a line named "IPv4 Address" , the number next to it is the IP address of the machine; 2. Under macOS system, click the Apple icon in the upper left corner of the screen, select "System Preferences", find the currently connected network in the "Network" option, and click the "Advanced" button , find the IP of the machine in the "TCP/IP" tab, etc.
 What should I do if my wifi shows no IP allocation?
Aug 30, 2023 am 11:58 AM
What should I do if my wifi shows no IP allocation?
Aug 30, 2023 am 11:58 AM
Solution to wifi showing no IP allocation: 1. Restart the device and router, turn off the Wi-Fi connection on the device, turn off the device, turn off the router, wait a few minutes, then reopen the router to connect to wifi; 2. Check the router settings and restart DHCP, make sure the DHCP function is enabled; 3. Reset network settings, which will delete all saved WiFi networks and passwords. Please make sure they are backed up before performing this operation; 4. Update the router firmware, log in to the router management interface, and find the firmware Update options and follow the prompts.
 How to solve if Edge browser is blocked by firewall?
Mar 13, 2024 pm 07:10 PM
How to solve if Edge browser is blocked by firewall?
Mar 13, 2024 pm 07:10 PM
How to solve the problem that the Edge browser is blocked by the firewall? Edge browser is Microsoft's own browser. Some users found that this browser was blocked by the firewall during use. So what's going on? Let this site give users a detailed introduction on how to recover the Edge browser if it is blocked by the firewall. How to restore the Edge browser if it is blocked by the firewall? 1. Check the firewall settings: - Click the "Start" button on the Windows taskbar, and then open "Settings". -In the Settings window, select Update & Security. -exist
 What does IP mean?
Jan 05, 2024 pm 01:34 PM
What does IP mean?
Jan 05, 2024 pm 01:34 PM
The common meanings of IP include "IP address", "intellectual property", "unique selling point" and "independence": 1. IP address is a digital identifier used to identify and locate equipment in computer networks; 2. Intellectual property , refers to the rights and interests enjoyed by people’s intellectual creations, including patents, trademarks, copyrights, trade secrets, etc.; 3. Unique selling points are the unique characteristics of a product or service that distinguish it from competitors and attract customers; 4. Independence refers to the ability of a country or region to make independent decisions and manage itself without external control or interference.






