Behind the scenes of Spring Data: Uncovering its powerful capabilities

php Xiaobian Xigua will take you to explore the powerful functions behind Spring Data. Spring Data is a project that provides comprehensive solutions for data access. It simplifies the development process of data access and provides support for multiple data storage technologies. Through Spring Data, developers can easily implement the development of the data access layer without caring about the details of the underlying data storage. This article will reveal the internal mechanisms and functions of Spring Data to help you better understand and apply this powerful data access framework.
spring Data creates an abstraction layer for interacting with different data stores. It does this by providing a common api that allows developers to use the same method to operate on different databases, regardless of their engines or dialects how. Spring Data supports a variety of relationships and NoSQL databases, including Mysql, mongoDB, Redis, postgresql and Cassandra.
Annotation driver:
Spring Data uses annotations to simplify data access. By using annotations (such as @Entity, @Table) on entity classes, Spring Data can automatically map objects to database tables or documents. The @Repository annotation is used to mark a DAO (Data Access Object) as a Spring-managed bean, allowing developers to directly manipulate the data.
Generate query:
Spring Data integrates with JPA (Java Persistence API), providing a standardized way to create and execute queries. By using JPA, Spring Data can automatically generate complex queries such as JOINs, sorting, and filters without developers having to write native sql. Spring Data also supports custom queries, allowing developers to write their own complex queries.
Transaction Management:
Spring Data takes full advantage of Spring's transaction management capabilities. It handles transactions transparently, ensuring atomicity and consistency of database operations. Transactions can be defined at the method or class level, and Spring Data will automatically handle transaction boundaries and rollbacks.
Other functions:
In addition to the above core functions, Spring Data also provides other functions that make it a powerful data access framework :
- Paging and sorting: Spring Data provides built-in support for paging and sorting query results to improve scalability and user experience.
- Data Validation: Spring Data integrates with the Bean Validation framework to enable developers to validate entity objects and enforce data integrity rules.
- Caching: Spring Data supports integration with caching providers such as Redis and Ehcache to improve performance on frequently accessed data.
Advantage:
Spring Data’s behind-the-scenes mechanisms provide the following benefits:
- Improving productivity: Spring Data's abstraction layer and annotation-driven approach simplify data access, allowing developers to focus on business logic rather than underlying database details.
- Portability: A common API with different databases enables developers to easily migrate applications without having to worry about changes in data storage technology.
- Improve efficiency: Using JPA to automatically generate queries and leveraging Spring's transaction management, Spring Data improves the efficiency of data access operations.
- Scalability: Spring Data supports scalable, high-throughput applications by providing features such as paging, caching, and data validation.
The above is the detailed content of Behind the scenes of Spring Data: Uncovering its powerful capabilities. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1386
1386
 52
52
 What does dao mean in java
Apr 21, 2024 am 02:08 AM
What does dao mean in java
Apr 21, 2024 am 02:08 AM
DAO (Data Access Object) in Java is used to separate application code and persistence layer, its advantages include: Separation: Independent from application logic, making it easier to modify it. Encapsulation: Hide database access details and simplify interaction with the database. Scalability: Easily expandable to support new databases or persistence technologies. With DAOs, applications can call methods to perform database operations such as create, read, update, and delete entities without directly dealing with database details.
 How to remove the write protection of a USB flash drive? Several simple and effective methods can help you do it
May 02, 2024 am 09:04 AM
How to remove the write protection of a USB flash drive? Several simple and effective methods can help you do it
May 02, 2024 am 09:04 AM
U disk is one of the commonly used storage devices in our daily work and life, but sometimes we encounter situations where the U disk is write-protected and cannot write data. This article will introduce several simple and effective methods to help you quickly remove the write protection of the USB flash drive and restore the normal use of the USB flash drive. Tool materials: System version: Windows1020H2, macOS BigSur11.2.3 Brand model: SanDisk UltraFlair USB3.0 flash drive, Kingston DataTraveler100G3USB3.0 flash drive Software version: DiskGenius5.4.2.1239, ChipGenius4.19.1225 1. Check the physical write protection switch of the USB flash drive on some USB flash drives Designed with
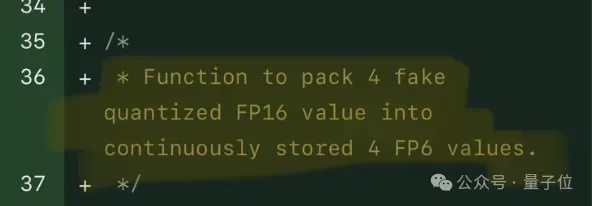 Single card running Llama 70B is faster than dual card, Microsoft forced FP6 into A100 | Open source
Apr 29, 2024 pm 04:55 PM
Single card running Llama 70B is faster than dual card, Microsoft forced FP6 into A100 | Open source
Apr 29, 2024 pm 04:55 PM
FP8 and lower floating point quantification precision are no longer the "patent" of H100! Lao Huang wanted everyone to use INT8/INT4, and the Microsoft DeepSpeed team started running FP6 on A100 without official support from NVIDIA. Test results show that the new method TC-FPx's FP6 quantization on A100 is close to or occasionally faster than INT4, and has higher accuracy than the latter. On top of this, there is also end-to-end large model support, which has been open sourced and integrated into deep learning inference frameworks such as DeepSpeed. This result also has an immediate effect on accelerating large models - under this framework, using a single card to run Llama, the throughput is 2.65 times higher than that of dual cards. one
 Usage of service layer in java
May 07, 2024 am 04:24 AM
Usage of service layer in java
May 07, 2024 am 04:24 AM
The Service layer in Java is responsible for business logic and business rules for executing applications, including processing business rules, data encapsulation, centralizing business logic and improving testability. In Java, the Service layer is usually designed as an independent module, interacts with the Controller and Repository layers, and is implemented through dependency injection, following steps such as creating an interface, injecting dependencies, and calling Service methods. Best practices include keeping it simple, using interfaces, avoiding direct manipulation of data, handling exceptions, and using dependency injection.
 What is the API interface for?
Apr 23, 2024 pm 01:51 PM
What is the API interface for?
Apr 23, 2024 pm 01:51 PM
An API interface is a specification for interaction between software components and is used to implement communication and data exchange between different applications or systems. The API interface acts as a "translator", converting the developer's instructions into computer language so that the applications can work together. Its advantages include convenient data sharing, simplified development, improved performance, enhanced security, improved productivity and interoperability.
 What does mysql database do?
Apr 22, 2024 pm 06:12 PM
What does mysql database do?
Apr 22, 2024 pm 06:12 PM
MySQL is a relational database management system that provides the following main functions: Data storage and management: Create and organize data, supporting various data types, primary keys, foreign keys, and indexes. Data query and retrieval: Use SQL language to query, filter and retrieve data, and optimize execution plans to improve efficiency. Data updates and modifications: Add, modify or delete data through INSERT, UPDATE, DELETE commands, supporting transactions to ensure consistency and rollback mechanisms to undo changes. Database management: Create and modify databases and tables, back up and restore data, and provide user management and permission control.
 What does schema mean in mysql
May 01, 2024 pm 08:33 PM
What does schema mean in mysql
May 01, 2024 pm 08:33 PM
Schema in MySQL is a logical structure used to organize and manage database objects (such as tables, views) to ensure data consistency, data access control and simplify database design. The functions of Schema include: 1. Data organization; 2. Data consistency; 3. Data access control; 4. Database design.
 Redis cache implementation principle
Apr 19, 2024 pm 10:36 PM
Redis cache implementation principle
Apr 19, 2024 pm 10:36 PM
The Redis caching mechanism is implemented through key-value storage, memory storage, expiration policies, data structures, replication, and persistence. It follows the steps of obtaining data, cache hit, cache miss, writing to cache, and updating cache to provide fast data access and high-performance caching services.




