How to set verification rules and verification text in access
Validation rules are expressions used to verify input data, and verification text is the prompt message displayed when the input value does not meet the verification rules. Setting validation rules involves entering expressions in the "Validation Rules" tab, while setting validation text requires entering prompt information in the "Validation Text" tab. Example: To verify that the value entered in the date of birth field is a valid date, set the validation rule to "=DateValue([date of birth])<=Date()" and set the validation text to "Please enter a valid date of birth" .
Set validation rules and validation text in Access
1. Validation rules
A validation rule is an expression used to verify whether the input data meets specific criteria. For example, to ensure that only numbers can be entered into a field, you can set a validation rule as: "IsNumeric([field name])".
Steps to set validation rules:
- Select the field for which you want to set validation rules.
- In the "Validation Rules" tab of the "Field Properties" pane, enter the expression.
- Click the "Verification Text" tab to enter the prompt message when verification fails.
2. Verification text
The verification text is the prompt message displayed when the entered value does not meet the verification rules. This helps the user understand the cause of the input error and correct the input.
Steps to set the verification text:
- In the "Validation Text" tab of the "Field Properties" pane, enter the prompt information.
- Make sure the validation rules have been set in the "Validation Rules" tab.
Example:
To set up a validation rule and validation text that ensures the value entered in the Date of Birth field is a valid date, follow these steps:
Validation rules:
<code>=DateValue([出生日期])<=Date()</code>
Validation text:
<code>请输入有效的出生日期。</code>
In this way, if the birth date entered by the user is greater than the current date, it will A prompt message appears prompting the user to enter a valid date of birth.
The above is the detailed content of How to set verification rules and verification text in access. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1359
1359
 52
52
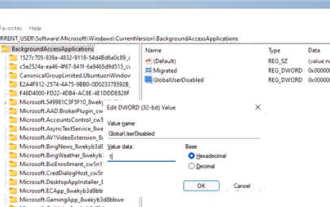 How to disable background applications in Windows 11_Windows 11 tutorial to disable background applications
May 07, 2024 pm 04:20 PM
How to disable background applications in Windows 11_Windows 11 tutorial to disable background applications
May 07, 2024 pm 04:20 PM
1. Open settings in Windows 11. You can use Win+I shortcut or any other method. 2. Go to the Apps section and click Apps & Features. 3. Find the application you want to prevent from running in the background. Click the three-dot button and select Advanced Options. 4. Find the [Background Application Permissions] section and select the desired value. By default, Windows 11 sets power optimization mode. It allows Windows to manage how applications work in the background. For example, once you enable battery saver mode to preserve battery, the system will automatically close all apps. 5. Select [Never] to prevent the application from running in the background. Please note that if you notice that the program is not sending you notifications, failing to update data, etc., you can
 How to convert deepseek pdf
Feb 19, 2025 pm 05:24 PM
How to convert deepseek pdf
Feb 19, 2025 pm 05:24 PM
DeepSeek cannot convert files directly to PDF. Depending on the file type, you can use different methods: Common documents (Word, Excel, PowerPoint): Use Microsoft Office, LibreOffice and other software to export as PDF. Image: Save as PDF using image viewer or image processing software. Web pages: Use the browser's "Print into PDF" function or the dedicated web page to PDF tool. Uncommon formats: Find the right converter and convert it to PDF. It is crucial to choose the right tools and develop a plan based on the actual situation.
 What does dao mean in java
Apr 21, 2024 am 02:08 AM
What does dao mean in java
Apr 21, 2024 am 02:08 AM
DAO (Data Access Object) in Java is used to separate application code and persistence layer, its advantages include: Separation: Independent from application logic, making it easier to modify it. Encapsulation: Hide database access details and simplify interaction with the database. Scalability: Easily expandable to support new databases or persistence technologies. With DAOs, applications can call methods to perform database operations such as create, read, update, and delete entities without directly dealing with database details.
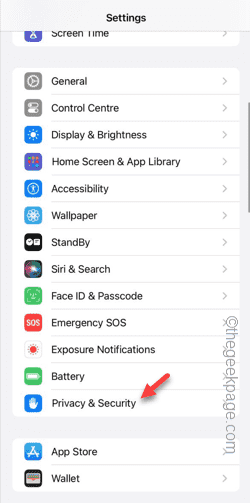 Can't allow access to camera and microphone in iPhone
Apr 23, 2024 am 11:13 AM
Can't allow access to camera and microphone in iPhone
Apr 23, 2024 am 11:13 AM
Are you getting "Unable to allow access to camera and microphone" when trying to use the app? Typically, you grant camera and microphone permissions to specific people on a need-to-provide basis. However, if you deny permission, the camera and microphone will not work and will display this error message instead. Solving this problem is very basic and you can do it in a minute or two. Fix 1 – Provide Camera, Microphone Permissions You can provide the necessary camera and microphone permissions directly in settings. Step 1 – Go to the Settings tab. Step 2 – Open the Privacy & Security panel. Step 3 – Turn on the “Camera” permission there. Step 4 – Inside, you will find a list of apps that have requested permission for your phone’s camera. Step 5 – Open the “Camera” of the specified app
 What does field mean in java
Apr 25, 2024 pm 10:18 PM
What does field mean in java
Apr 25, 2024 pm 10:18 PM
In Java, a "field" is a data member in a class or interface that is used to store data or state. The properties of field include: type (can be any Java data type), access rights, static (belongs to a class rather than an instance), final (immutable) and transient (not serialized). Field is used to store state information of a class or interface, such as storing object data and maintaining object state.
 How does the Java reflection mechanism modify the behavior of a class?
May 03, 2024 pm 06:15 PM
How does the Java reflection mechanism modify the behavior of a class?
May 03, 2024 pm 06:15 PM
The Java reflection mechanism allows programs to dynamically modify the behavior of classes without modifying the source code. By operating the Class object, you can create instances through newInstance(), modify private field values, call private methods, etc. Reflection should be used with caution, however, as it can cause unexpected behavior and security issues, and has a performance overhead.
 How to read dbf file in oracle
May 10, 2024 am 01:27 AM
How to read dbf file in oracle
May 10, 2024 am 01:27 AM
Oracle can read dbf files through the following steps: create an external table and reference the dbf file; query the external table to retrieve data; import the data into the Oracle table.
 What does a memory stick look like?
Apr 21, 2024 pm 01:01 PM
What does a memory stick look like?
Apr 21, 2024 pm 01:01 PM
What does a computer memory module look like? This is an overview of the graphics card and memory module in the computer. The computer's independent graphics card is inserted into the graphics card slot, with a fan, and the memory module is inside the memory module slot on the computer's motherboard, shaped like a green rectangle. Laptop memory modules are different from desktop memory modules, and they cannot be used interchangeably. Appearance difference 1: Desktop memory, slender, 13-14 cm in length. 2: Notebook memory is shorter, about five centimeters. Memory is the bridge in the computer, responsible for data exchange between the processor and hardware such as hard disk, motherboard, and graphics card. The red circle on the way is the memory stick, next to the CPU fan and plugged into the memory stick. Look, a computer memory stick looks like this. Use a screwdriver to open the cover of the desktop computer. The red circle in the middle is the memory module. What is a memory stick?




