 Java
Java
 javaTutorial
javaTutorial
 How does Java security mechanism deal with different types of security threats?
How does Java security mechanism deal with different types of security threats?
How does Java security mechanism deal with different types of security threats?
Java provides multiple layers of security mechanisms to deal with security threats, including: Encryption and signing: Protect data from unauthorized access and tampering. Permission control: Restrict application access to system resources. Sandbox: Isolate applications to reduce the impact of malicious code. Code Signing: Verify the source and integrity of your code.
Java security mechanism responds to different types of security threats
As a popular programming language, Java provides a multi-layer security mechanism to deal with various security threats. These mechanisms are designed to protect applications and systems from malicious code, data leakage, and identity theft.
Encryption and Signature
Java provides encryption and signature APIs, such as java.security.Signature and java.security.MessageDigest . These APIs can be used to encrypt and sign data, protecting it from unauthorized access and tampering.
Permission Control
Java's permission control model allows applications to request permissions for specific operations. For example, an application can use java.lang.SecurityManager to restrict access to file system or network resources.
Sandbox
The Java sandboxing mechanism can provide additional protection by isolating applications in a restricted environment. This mechanism limits an application's access to system resources, thereby reducing the potential impact of malicious code.
Code Signing
The Java code signing mechanism allows developers to sign their code to verify its origin and integrity. When the application loads, the Java runtime verifies the signature and prevents unsigned or tampered code from executing.
Practical Case: Protecting Sensitive Data
The following code shows an example of using Java Encryption and Signature API to protect sensitive data:
import java.security.Signature;
import java.security.MessageDigest;
public class SensitiveDataProtection {
private static void encryptData(byte[] data) {
// 使用 AES-256 对数据进行加密
// ...
// 将加密后的数据写入文件或其他存储
// ...
}
private static boolean verifyData(byte[] data, byte[] signature) {
// 从文件中读取加密后的数据
// ...
// 使用 RSA 算法对数据进行签名验证
Signature verifier = Signature.getInstance("SHA256withRSA");
verifier.initVerify(publicKey);
verifier.update(data);
return verifier.verify(signature);
}
// ...
} Above In the example, the encryptData method uses AES-256 to encrypt sensitive data and then stores it in a secure location. The verifyData method uses the RSA algorithm to verify the authenticity and integrity of the data, and returns a Boolean value indicating whether the verification was successful.
The above is the detailed content of How does Java security mechanism deal with different types of security threats?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1385
1385
 52
52
 Break or return from Java 8 stream forEach?
Feb 07, 2025 pm 12:09 PM
Break or return from Java 8 stream forEach?
Feb 07, 2025 pm 12:09 PM
Java 8 introduces the Stream API, providing a powerful and expressive way to process data collections. However, a common question when using Stream is: How to break or return from a forEach operation? Traditional loops allow for early interruption or return, but Stream's forEach method does not directly support this method. This article will explain the reasons and explore alternative methods for implementing premature termination in Stream processing systems. Further reading: Java Stream API improvements Understand Stream forEach The forEach method is a terminal operation that performs one operation on each element in the Stream. Its design intention is
 How to convert XML files to PDF on your phone?
Apr 02, 2025 pm 10:12 PM
How to convert XML files to PDF on your phone?
Apr 02, 2025 pm 10:12 PM
It is impossible to complete XML to PDF conversion directly on your phone with a single application. It is necessary to use cloud services, which can be achieved through two steps: 1. Convert XML to PDF in the cloud, 2. Access or download the converted PDF file on the mobile phone.
 Recommended XML formatting tool
Apr 02, 2025 pm 09:03 PM
Recommended XML formatting tool
Apr 02, 2025 pm 09:03 PM
XML formatting tools can type code according to rules to improve readability and understanding. When selecting a tool, pay attention to customization capabilities, handling of special circumstances, performance and ease of use. Commonly used tool types include online tools, IDE plug-ins, and command-line tools.
 Java Program to Find the Volume of Capsule
Feb 07, 2025 am 11:37 AM
Java Program to Find the Volume of Capsule
Feb 07, 2025 am 11:37 AM
Capsules are three-dimensional geometric figures, composed of a cylinder and a hemisphere at both ends. The volume of the capsule can be calculated by adding the volume of the cylinder and the volume of the hemisphere at both ends. This tutorial will discuss how to calculate the volume of a given capsule in Java using different methods. Capsule volume formula The formula for capsule volume is as follows: Capsule volume = Cylindrical volume Volume Two hemisphere volume in, r: The radius of the hemisphere. h: The height of the cylinder (excluding the hemisphere). Example 1 enter Radius = 5 units Height = 10 units Output Volume = 1570.8 cubic units explain Calculate volume using formula: Volume = π × r2 × h (4
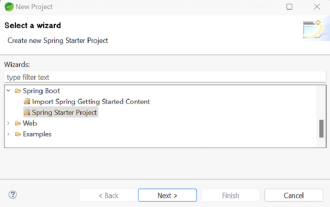 How to Run Your First Spring Boot Application in Spring Tool Suite?
Feb 07, 2025 pm 12:11 PM
How to Run Your First Spring Boot Application in Spring Tool Suite?
Feb 07, 2025 pm 12:11 PM
Spring Boot simplifies the creation of robust, scalable, and production-ready Java applications, revolutionizing Java development. Its "convention over configuration" approach, inherent to the Spring ecosystem, minimizes manual setup, allo
 Create the Future: Java Programming for Absolute Beginners
Oct 13, 2024 pm 01:32 PM
Create the Future: Java Programming for Absolute Beginners
Oct 13, 2024 pm 01:32 PM
Java is a popular programming language that can be learned by both beginners and experienced developers. This tutorial starts with basic concepts and progresses through advanced topics. After installing the Java Development Kit, you can practice programming by creating a simple "Hello, World!" program. After you understand the code, use the command prompt to compile and run the program, and "Hello, World!" will be output on the console. Learning Java starts your programming journey, and as your mastery deepens, you can create more complex applications.
 Java Made Simple: A Beginner's Guide to Programming Power
Oct 11, 2024 pm 06:30 PM
Java Made Simple: A Beginner's Guide to Programming Power
Oct 11, 2024 pm 06:30 PM
Java Made Simple: A Beginner's Guide to Programming Power Introduction Java is a powerful programming language used in everything from mobile applications to enterprise-level systems. For beginners, Java's syntax is simple and easy to understand, making it an ideal choice for learning programming. Basic Syntax Java uses a class-based object-oriented programming paradigm. Classes are templates that organize related data and behavior together. Here is a simple Java class example: publicclassPerson{privateStringname;privateintage;
 How to evaluate the destructive power of the website after discovering suspicious Trojan files?
Apr 01, 2025 am 08:39 AM
How to evaluate the destructive power of the website after discovering suspicious Trojan files?
Apr 01, 2025 am 08:39 AM
When a suspicious Trojan file is found on the website, how to evaluate its destructive power? Recently, a suspicious Trojan file was found while performing a security scan on the website. ...



