缅怀:Photoshop制作国难日哀悼海报教程
缅怀:Photoshop制作国难日哀悼海报教程。
相关Photoshop教程文章:天佑中华 PS打造众志成城抗震海报
先看一下最终效果:  新建一个文件,然后填充为黑色,再新建一个图层,自己用矩形工具以及多边形工具绘制出我们的国旗。
新建一个文件,然后填充为黑色,再新建一个图层,自己用矩形工具以及多边形工具绘制出我们的国旗。 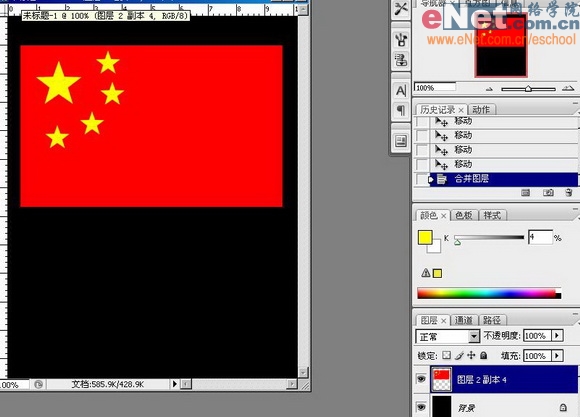

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How to ensure high availability of MongoDB on Debian
Apr 02, 2025 am 07:21 AM
How to ensure high availability of MongoDB on Debian
Apr 02, 2025 am 07:21 AM
This article describes how to build a highly available MongoDB database on a Debian system. We will explore multiple ways to ensure data security and services continue to operate. Key strategy: ReplicaSet: ReplicaSet: Use replicasets to achieve data redundancy and automatic failover. When a master node fails, the replica set will automatically elect a new master node to ensure the continuous availability of the service. Data backup and recovery: Regularly use the mongodump command to backup the database and formulate effective recovery strategies to deal with the risk of data loss. Monitoring and Alarms: Deploy monitoring tools (such as Prometheus, Grafana) to monitor the running status of MongoDB in real time, and
 PostgreSQL monitoring method under Debian
Apr 02, 2025 am 07:27 AM
PostgreSQL monitoring method under Debian
Apr 02, 2025 am 07:27 AM
This article introduces a variety of methods and tools to monitor PostgreSQL databases under the Debian system, helping you to fully grasp database performance monitoring. 1. Use PostgreSQL to build-in monitoring view PostgreSQL itself provides multiple views for monitoring database activities: pg_stat_activity: displays database activities in real time, including connections, queries, transactions and other information. pg_stat_replication: Monitors replication status, especially suitable for stream replication clusters. pg_stat_database: Provides database statistics, such as database size, transaction commit/rollback times and other key indicators. 2. Use log analysis tool pgBadg
 Can the Python interpreter be deleted in Linux system?
Apr 02, 2025 am 07:00 AM
Can the Python interpreter be deleted in Linux system?
Apr 02, 2025 am 07:00 AM
Regarding the problem of removing the Python interpreter that comes with Linux systems, many Linux distributions will preinstall the Python interpreter when installed, and it does not use the package manager...
 How to teach computer novice programming basics in project and problem-driven methods within 10 hours?
Apr 02, 2025 am 07:18 AM
How to teach computer novice programming basics in project and problem-driven methods within 10 hours?
Apr 02, 2025 am 07:18 AM
How to teach computer novice programming basics within 10 hours? If you only have 10 hours to teach computer novice some programming knowledge, what would you choose to teach...
 What is the impact of Debian Message on network configuration
Apr 02, 2025 am 07:51 AM
What is the impact of Debian Message on network configuration
Apr 02, 2025 am 07:51 AM
The network configuration of the Debian system is mainly implemented through the /etc/network/interfaces file, which defines network interface parameters, such as IP address, gateway, and DNS server. Debian systems usually use ifup and ifdown commands to start and stop network interfaces. By modifying the ifeline in the interfaces file, you can set a static IP or use DHCP to dynamically obtain the IP address. It should be noted that Debian12 and subsequent versions no longer use NetworkManager by default, so other command-line tools, such as IP commands, may be required to manage network interfaces. You can edit /etc/netwo
 How to get news data bypassing Investing.com's anti-crawler mechanism?
Apr 02, 2025 am 07:03 AM
How to get news data bypassing Investing.com's anti-crawler mechanism?
Apr 02, 2025 am 07:03 AM
Understanding the anti-crawling strategy of Investing.com Many people often try to crawl news data from Investing.com (https://cn.investing.com/news/latest-news)...
 How to solve the problem of Pylance type detection of custom decorators in Python?
Apr 02, 2025 am 06:42 AM
How to solve the problem of Pylance type detection of custom decorators in Python?
Apr 02, 2025 am 06:42 AM
Pylance type detection problem solution when using custom decorator In Python programming, decorator is a powerful tool that can be used to add rows...
 How to ensure the security of fetchdebian downloads
Apr 02, 2025 am 07:39 AM
How to ensure the security of fetchdebian downloads
Apr 02, 2025 am 07:39 AM
Downloading software from official Debian or reliable sources is crucial. The following steps and suggestions can effectively ensure the security of the downloaded Debian system or software package: 1. Verify the integrity of the software package After downloading the Debian image, be sure to use MD5 or SHA256 and other checksums to verify its integrity to prevent malicious tampering. 2. Choose a secure mirror source to always download from the Debian official website or a reputable third-party mirror site. Priority is given to official certification or mirroring sources provided by large institutions. 3. Keep the system updates and installation immediately after running sudoaptupdate&&sudoaptupgrade to fix potential security vulnerabilities. It is recommended to install unattend






