GitHub 上有哪些安全相关的 Python 项目值得一读?
包括但不限于binary web
回复内容:
网络https://github.com/dloss/python-pentest-tools sqlmap github 上有人专门整理过列表(dloss/python-pentest-tools · GitHub),虽然并不是很完备,但总体上还是不错的一份单子。Scapy: send, sniff and dissect and forge network packets. Usable interactively or as a library
pypcap, Pcapy and pylibpcap: several different Python bindings for libpcap
libdnet: low-level networking routines, including interface lookup and Ethernet frame transmission
dpkt: fast, simple packet creation/parsing, with definitions for the basic TCP/IP protocols
Impacket: craft and decode network packets. Includes support for higher-level protocols such as NMB and SMB
pynids: libnids wrapper offering sniffing, IP defragmentation, TCP stream reassembly and port scan detection
Dirtbags py-pcap: read pcap files without libpcap
flowgrep: grep through packet payloads using regular expressions
Knock Subdomain Scan, enumerate subdomains on a target domain through a wordlist
Mallory, extensible TCP/UDP man-in-the-middle proxy, supports modifying non-standard protocols on the fly
Pytbull: flexible IDS/IPS testing framework (shipped with more than 300 tests)
调试和逆向工程Paimei: reverse engineering framework, includes PyDBG, PIDA, pGRAPH
Immunity Debugger: scriptable GUI and command line debugger
mona.py: PyCommand for Immunity Debugger that replaces and improves on pvefindaddr
IDAPython: IDA Pro plugin that integrates the Python programming language, allowing scripts to run in IDA Pro
PyEMU: fully scriptable IA-32 emulator, useful for malware analysis
pefile: read and work with Portable Executable (aka PE) files
pydasm: Python interface to the libdasm x86 disassembling library
PyDbgEng: Python wrapper for the Microsoft Windows Debugging Engine
uhooker: intercept calls to API calls inside DLLs, and also arbitrary addresses within the executable file in memory
diStorm: disassembler library for AMD64, licensed under the BSD license
python-ptrace: debugger using ptrace (Linux, BSD and Darwin system call to trace processes) written in Python
vdb / vtrace: vtrace is a cross-platform process debugging API implemented in python, and vdb is a debugger which uses it
Androguard: reverse engineering and analysis of Android application
FuzzingSulley: fuzzer development and fuzz testing framework consisting of multiple extensible components
Peach Fuzzing Platform: extensible fuzzing framework for generation and mutation based fuzzing (v2 was written in Python)
antiparser: fuzz testing and fault injection API
TAOF, (The Art of Fuzzing) including ProxyFuzz, a man-in-the-middle non-deterministic network fuzzer
untidy: general purpose XML fuzzer
Powerfuzzer: highly automated and fully customizable web fuzzer (HTTP protocol based application fuzzer)
SMUDGE
Mistress: probe file formats on the fly and protocols with malformed data, based on pre-defined patterns
Fuzzbox: multi-codec media fuzzer
Forensic Fuzzing Tools: generate fuzzed files, fuzzed file systems, and file systems containing fuzzed files in order to test the robustness of forensics tools and examination systems
Windows IPC Fuzzing Tools: tools used to fuzz applications that use Windows Interprocess Communication mechanisms
WSBang: perform automated security testing of SOAP based web services
Construct: library for parsing and building of data structures (binary or textual). Define your data structures in a declarative manner
fuzzer.py (feliam): simple fuzzer by Felipe Andres Manzano
Fusil: Python library used to write fuzzing programs
WebRequests: elegant and simple HTTP library, built for human beings
HTTPie: human-friendly cURL-like command line HTTP client
ProxMon: processes proxy logs and reports discovered issues
WSMap: find web service endpoints and discovery files
Twill: browse the Web from a command-line interface. Supports automated Web testing
Ghost.py: webkit web client written in Python
Windmill: web testing tool designed to let you painlessly automate and debug your web application
FunkLoad: functional and load web tester
spynner: Programmatic web browsing module for Python with Javascript/AJAX support
python-spidermonkey: bridge to the Mozilla SpiderMonkey JavaScript engine; allows for the evaluation and calling of Javascript scripts and functions
mitmproxy: SSL-capable, intercepting HTTP proxy. Console interface allows traffic flows to be inspected and edited on the fly
pathod / pathoc: pathological daemon/client for tormenting HTTP clients and servers
取证Volatility: extract digital artifacts from volatile memory (RAM) samples
LibForensics: library for developing digital forensics applications
TrIDLib, identify file types from their binary signatures. Now includes Python binding
aft: Android forensic toolkit
恶意程序分析pyew: command line hexadecimal editor and disassembler, mainly to analyze malware
Exefilter: filter file formats in e-mails, web pages or files. Detects many common file formats and can remove active content
pyClamAV: add virus detection capabilities to your Python software
jsunpack-n, generic JavaScript unpacker: emulates browser functionality to detect exploits that target browser and browser plug-in vulnerabilities
yara-python: identify and classify malware samples
phoneyc: pure Python honeyclient implementation
Didier Stevens' PDF tools: analyse, identify and create PDF files (includes PDFiD, pdf-parserand make-pdf and mPDF)
Opaf: Open PDF Analysis Framework. Converts PDF to an XML tree that can be analyzed and modified.
Origapy: Python wrapper for the Origami Ruby module which sanitizes PDF files
pyPDF: pure Python PDF toolkit: extract info, spilt, merge, crop, encrypt, decrypt…
PDFMiner: extract text from PDF files
python-poppler-qt4: Python binding for the Poppler PDF library, including Qt4 support
MiscInlineEgg: toolbox of classes for writing small assembly programs in Python
Exomind: framework for building decorated graphs and developing open-source intelligence modules and ideas, centered on social network services, search engines and instant messaging
RevHosts: enumerate virtual hosts for a given IP address
simplejson: JSON encoder/decoder, e.g. to use Google's AJAX API
PyMangle: command line tool and a python library used to create word lists for use with other penetration testing tools
Hachoir: view and edit a binary stream field by field
py-mangle: command line tool and a python library used to create word lists for use with other penetration testing tools
其他有用的py库和工具
BpythonIPython: enhanced interactive Python shell with many features for object introspection, system shell access, and its own special command system
Beautiful Soup: HTML parser optimized for screen-scraping
matplotlib: make 2D plots of arrays
Mayavi: 3D scientific data visualization and plotting
RTGraph3D: create dynamic graphs in 3D
Twisted: event-driven networking engine
Suds: lightweight SOAP client for consuming Web Services
M2Crypto: most complete OpenSSL wrapper
NetworkX: graph library (edges, nodes)
Pandas: library providing high-performance, easy-to-use data structures and data analysis tools
pyparsing: general parsing module
lxml: most feature-rich and easy-to-use library for working with XML and HTML in the Python language
Whoosh: fast, featureful full-text indexing and searching library implemented in pure Python
Pexpect: control and automate other programs, similar to Don Libes `Expect` system
Sikuli, visual technology to search and automate GUIs using screenshots. Scriptable inJython
PyQt and PySide: Python bindings for the Qt application framework and GUI library
另外需要额外提一点,大多数的 python 安全项目只适合看一看,没必要读一读,因为很多安全项目的工程架构、编码规范其实都一般般,了其概要便足够了。 是不是python没有考察,自己总结的一份关于信息安全的开源工具集。
WALA:对java字节码和javascript提供静态分析
PIXY:php静态分析工具,(污点分析)
clang:编译器的前端工作,负责词法分析和语法分析,生成语法树。
llvm:编译器的后端工作,负责中间码的生成,代码优化,机器码的生成。
klee: 适用于c语言,静态符号执行工具,建立在llvm之上。
magic:静态模型检测工具,适用于c语言
blast:静态模型检测工具,适用于c语言
java pathfinder: 静态模型检测工具,适用于java语言
Saturn(stanford): 基于定理证明的静态漏洞检测工具,适用于c语言
ESC/JAVA:基于定理证明的静态漏洞检测工具,适用于java
Peach:大名鼎鼎的fuzz框架。
Sulley(2012):新一代fuzz框架,python实现。
Argos:动态污点技术,用于主机蜜罐,检测0day攻击。
BitBlaze: 静态分析组件vine和动态分析组件temu都是开源。但是线上动态符号执行组件不开源。
valgrind:开源虚拟机,用于动态二进制分析。拥有内存分配分析和线程分析等等。动态二进制插桩的代表。只能实现用户态跟踪
TaintDroid: android动态污点分析工具
BAP:基于二进制可执行程序反汇编的漏洞模式检测工具。OCaml语言编写。
BinNavi:基于二进制可执行程序反汇编的漏洞模式检测工具。不能反汇编,需要借助IDA Pro对二进制文件反汇编。
Z3:微软开源的约束求解器。具有跨平台特性
STP:MIT开源协议的开源软件。在符号执行中广泛应用。但只能运行在Linux平台下。 逆向工程、二进制分析的工具:
qira BinaryAnalysisPlatform/qira · GitHub
angr angr/angr · GitHub the fuck greysign/thefuck · GitHub
没有理由不推荐它…… http://awesome-python.com/
这个网站上面列出的所有的库,都是一些优秀的第三方Python库,大部分托管在github上,都值得去认真阅读。 从题主问题出发,安全+值得读+python
requests不错,
创宇cos推荐sqlmap,
其他答案也有不错的工具。
好工具不一定值得读?!
本想推荐androguard 不过没读过!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
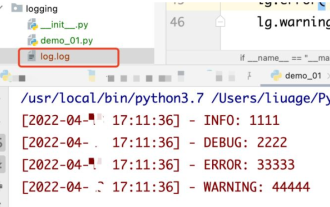 How to use python+Flask to realize real-time update and display of logs on web pages
May 17, 2023 am 11:07 AM
How to use python+Flask to realize real-time update and display of logs on web pages
May 17, 2023 am 11:07 AM
1. Log output to file using module: logging can generate a custom level log, and can output the log to a specified path. Log level: debug (debug log) = 5) {clearTimeout (time) // If all results obtained 10 consecutive times are empty Log clearing scheduled task}return}if(data.log_type==2){//If a new log is obtained for(i=0;i
 How to use Nginx web server caddy
May 30, 2023 pm 12:19 PM
How to use Nginx web server caddy
May 30, 2023 pm 12:19 PM
Introduction to Caddy Caddy is a powerful and highly scalable web server that currently has 38K+ stars on Github. Caddy is written in Go language and can be used for static resource hosting and reverse proxy. Caddy has the following main features: Compared with the complex configuration of Nginx, its original Caddyfile configuration is very simple; it can dynamically modify the configuration through the AdminAPI it provides; it supports automated HTTPS configuration by default, and can automatically apply for HTTPS certificates and configure it; it can be expanded to data Tens of thousands of sites; can be executed anywhere with no additional dependencies; written in Go language, memory safety is more guaranteed. First of all, we install it directly in CentO
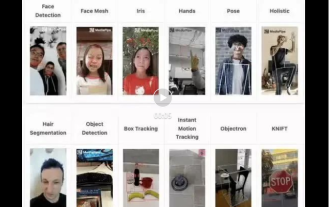 Real-time protection against face-blocking barrages on the web (based on machine learning)
Jun 10, 2023 pm 01:03 PM
Real-time protection against face-blocking barrages on the web (based on machine learning)
Jun 10, 2023 pm 01:03 PM
Face-blocking barrage means that a large number of barrages float by without blocking the person in the video, making it look like they are floating from behind the person. Machine learning has been popular for several years, but many people don’t know that these capabilities can also be run in browsers. This article introduces the practical optimization process in video barrages. At the end of the article, it lists some applicable scenarios for this solution, hoping to open it up. Some ideas. mediapipeDemo (https://google.github.io/mediapipe/) demonstrates the mainstream implementation principle of face-blocking barrage on-demand up upload. The server background calculation extracts the portrait area in the video screen, and converts it into svg storage while the client plays the video. Download svg from the server and combine it with barrage, portrait
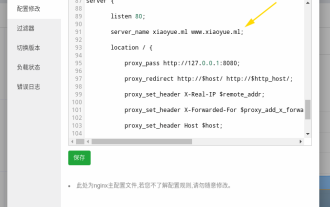 How to configure nginx to ensure that the frps server and web share port 80
Jun 03, 2023 am 08:19 AM
How to configure nginx to ensure that the frps server and web share port 80
Jun 03, 2023 am 08:19 AM
First of all, you will have a doubt, what is frp? Simply put, frp is an intranet penetration tool. After configuring the client, you can access the intranet through the server. Now my server has used nginx as the website, and there is only one port 80. So what should I do if the FRP server also wants to use port 80? After querying, this can be achieved by using nginx's reverse proxy. To add: frps is the server, frpc is the client. Step 1: Modify the nginx.conf configuration file in the server and add the following parameters to http{} in nginx.conf, server{listen80
 How to implement form validation for web applications using Golang
Jun 24, 2023 am 09:08 AM
How to implement form validation for web applications using Golang
Jun 24, 2023 am 09:08 AM
Form validation is a very important link in web application development. It can check the validity of the data before submitting the form data to avoid security vulnerabilities and data errors in the application. Form validation for web applications can be easily implemented using Golang. This article will introduce how to use Golang to implement form validation for web applications. 1. Basic elements of form validation Before introducing how to implement form validation, we need to know what the basic elements of form validation are. Form elements: form elements are
 Using Jetty7 for Web server processing in Java API development
Jun 18, 2023 am 10:42 AM
Using Jetty7 for Web server processing in Java API development
Jun 18, 2023 am 10:42 AM
Using Jetty7 for Web Server Processing in JavaAPI Development With the development of the Internet, the Web server has become the core part of application development and is also the focus of many enterprises. In order to meet the growing business needs, many developers choose to use Jetty for web server development, and its flexibility and scalability are widely recognized. This article will introduce how to use Jetty7 in JavaAPI development for We
 Is PHP front-end or back-end in web development?
Mar 24, 2024 pm 02:18 PM
Is PHP front-end or back-end in web development?
Mar 24, 2024 pm 02:18 PM
PHP belongs to the backend in web development. PHP is a server-side scripting language, mainly used to process server-side logic and generate dynamic web content. Compared with front-end technology, PHP is more used for back-end operations such as interacting with databases, processing user requests, and generating page content. Next, specific code examples will be used to illustrate the application of PHP in back-end development. First, let's look at a simple PHP code example for connecting to a database and querying data:
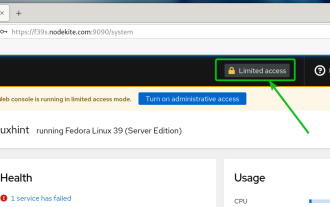 How to enable administrative access from the cockpit web UI
Mar 20, 2024 pm 06:56 PM
How to enable administrative access from the cockpit web UI
Mar 20, 2024 pm 06:56 PM
Cockpit is a web-based graphical interface for Linux servers. It is mainly intended to make managing Linux servers easier for new/expert users. In this article, we will discuss Cockpit access modes and how to switch administrative access to Cockpit from CockpitWebUI. Content Topics: Cockpit Entry Modes Finding the Current Cockpit Access Mode Enable Administrative Access for Cockpit from CockpitWebUI Disabling Administrative Access for Cockpit from CockpitWebUI Conclusion Cockpit Entry Modes The cockpit has two access modes: Restricted Access: This is the default for the cockpit access mode. In this access mode you cannot access the web user from the cockpit






