 Web Front-end
Web Front-end
 JS Tutorial
JS Tutorial
 What security vulnerabilities exist when using timing-attack in node applications?
What security vulnerabilities exist when using timing-attack in node applications?
What security vulnerabilities exist when using timing-attack in node applications?
This article analyzes the timing-attack security vulnerability of node applications based on the principle. Friends who are interested can read it for reference.
Preface
If you have encountered an eslint error Potential timing attack in your project, don’t ignore it! This is a security issue: timing attacks.
eslint Error Reason
First of all, eslint introduces a plug-in called eslint-plugin-security. This plug-in helps identify potential security issues, but it can also cause false positives. Attached Plug-in source code address.
var keywords = '((' + [
'password',
'secret',
'api',
'apiKey',
'token',
'auth',
'pass',
'hash'
].join(')|(') + '))';
var re = new RegExp('^' + keywords + '$', 'im');
function containsKeyword (node) {
if (node.type === 'Identifier') {
if (re.test(node.name)) return true;
}
return
}
if (node.test.operator === '==' || node.test.operator === '===' || node.test.operator === '!=' || node.test.operator === '!==') {
// 在这里 console 出错误
}First of all, this plug-in will determine whether the operator this time is ==, ===,! =,! ==One of them, secondly check whether the identifier (field name) contains the special string password, secret, api, apiKey, token, auth, pass, hash. If both conditions are met at the same time, eslint will compile and report an error Potential timing attack .
attack definition
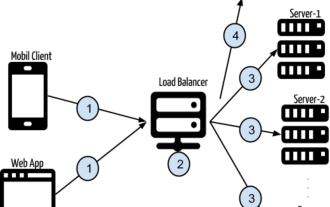
timing attack: Timing attack, which belongs to side channel attack/side channel attack. Side channel attack refers to the use of information outside the channel, such as encryption and decryption. The attack method is based on the data, data comparison time, ciphertext transmission traffic and channels, which is equivalent to "making innuendo".
Attack point
First let’s talk about the principle of js comparing the size of two strings:
Determine whether the string length is is 0. If it is 0, the result can be directly compared; otherwise, go to the second step.
Strings are composed of characters and are compared by the charCode of each character.
In the second step, as long as one character is different, return false, and the remaining characters will not be compared.
The comparison of single characters is very fast. The attacker can refine the measurement time accuracy to microseconds and deduce the starting character from the difference in response time. In this way By experimenting again and again or writing a script in Python to run, you can try out the correct password, and the difficulty of password cracking is also reduced a lot.
Vulnerable writing method
if (user.password === password) {
return { state: true }; // 登录成功
}Defensive measures
Each different input will cause the processing time to be different. To prevent it, we need to make the string comparison take the same amount of time regardless of the password entered.
Writing that is not vulnerable to attacks
The length of each password in the system is fixed. Each time the password is compared to see if it is the same, the length of the correct password is used as the number of comparisons, and XOR is used to compare each character. Check whether the Unicode encodings are equal, and store each comparison result in an array, and finally determine whether each element of the array is 0 (0 means the two characters are the same).
// psdReceived 为用户输入密码;
// psdDb 为系统中存储的正确用户密码
const correctUser = (psdDb, psdReceived) => {
const state = [];
for (let i = 0; i < psdDb.length; ++i) {
if (!psdReceived[i]) {
state.push(false);
} else {
state.push(psdReceived.charCodeAt(i) ^ psdDb.charCodeAt(i));
}
}
return state.length !== 0 && state.every(item => !item);
}Three-party package recommendation
You can also use the cryptiles npm module to solve this problem
import cryptiles from 'cryptiles'; ...... return cryptiles.fixedTimeCimparison(passwordFromDb, passwordReceived);
The above is what I compiled for everyone. I hope it will be helpful to everyone in the future.
Related articles:
NodeJS parent process and child process resource sharing principles and implementation methods
How to upload images and files in vue Sample code
vue axios form submission example of uploading images
The above is the detailed content of What security vulnerabilities exist when using timing-attack in node applications?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How to delete node in nvm
Dec 29, 2022 am 10:07 AM
How to delete node in nvm
Dec 29, 2022 am 10:07 AM
How to delete node with nvm: 1. Download "nvm-setup.zip" and install it on the C drive; 2. Configure environment variables and check the version number through the "nvm -v" command; 3. Use the "nvm install" command Install node; 4. Delete the installed node through the "nvm uninstall" command.
 How to use express to handle file upload in node project
Mar 28, 2023 pm 07:28 PM
How to use express to handle file upload in node project
Mar 28, 2023 pm 07:28 PM
How to handle file upload? The following article will introduce to you how to use express to handle file uploads in the node project. I hope it will be helpful to you!
 How to do Docker mirroring of Node service? Detailed explanation of extreme optimization
Oct 19, 2022 pm 07:38 PM
How to do Docker mirroring of Node service? Detailed explanation of extreme optimization
Oct 19, 2022 pm 07:38 PM
During this period, I was developing a HTML dynamic service that is common to all categories of Tencent documents. In order to facilitate the generation and deployment of access to various categories, and to follow the trend of cloud migration, I considered using Docker to fix service content and manage product versions in a unified manner. . This article will share the optimization experience I accumulated in the process of serving Docker for your reference.
 An in-depth analysis of Node's process management tool 'pm2”
Apr 03, 2023 pm 06:02 PM
An in-depth analysis of Node's process management tool 'pm2”
Apr 03, 2023 pm 06:02 PM
This article will share with you Node's process management tool "pm2", and talk about why pm2 is needed, how to install and use pm2, I hope it will be helpful to everyone!
 Pi Node Teaching: What is a Pi Node? How to install and set up Pi Node?
Mar 05, 2025 pm 05:57 PM
Pi Node Teaching: What is a Pi Node? How to install and set up Pi Node?
Mar 05, 2025 pm 05:57 PM
Detailed explanation and installation guide for PiNetwork nodes This article will introduce the PiNetwork ecosystem in detail - Pi nodes, a key role in the PiNetwork ecosystem, and provide complete steps for installation and configuration. After the launch of the PiNetwork blockchain test network, Pi nodes have become an important part of many pioneers actively participating in the testing, preparing for the upcoming main network release. If you don’t know PiNetwork yet, please refer to what is Picoin? What is the price for listing? Pi usage, mining and security analysis. What is PiNetwork? The PiNetwork project started in 2019 and owns its exclusive cryptocurrency Pi Coin. The project aims to create a one that everyone can participate
 Let's talk about how to use pkg to package Node.js projects into executable files.
Dec 02, 2022 pm 09:06 PM
Let's talk about how to use pkg to package Node.js projects into executable files.
Dec 02, 2022 pm 09:06 PM
How to package nodejs executable file with pkg? The following article will introduce to you how to use pkg to package a Node project into an executable file. I hope it will be helpful to you!
 Token-based authentication with Angular and Node
Sep 01, 2023 pm 02:01 PM
Token-based authentication with Angular and Node
Sep 01, 2023 pm 02:01 PM
Authentication is one of the most important parts of any web application. This tutorial discusses token-based authentication systems and how they differ from traditional login systems. By the end of this tutorial, you will see a fully working demo written in Angular and Node.js. Traditional Authentication Systems Before moving on to token-based authentication systems, let’s take a look at traditional authentication systems. The user provides their username and password in the login form and clicks Login. After making the request, authenticate the user on the backend by querying the database. If the request is valid, a session is created using the user information obtained from the database, and the session information is returned in the response header so that the session ID is stored in the browser. Provides access to applications subject to
 What to do if npm node gyp fails
Dec 29, 2022 pm 02:42 PM
What to do if npm node gyp fails
Dec 29, 2022 pm 02:42 PM
npm node gyp fails because "node-gyp.js" does not match the version of "Node.js". The solution is: 1. Clear the node cache through "npm cache clean -f"; 2. Through "npm install -g n" Install the n module; 3. Install the "node v12.21.0" version through the "n v12.21.0" command.





