Website load balancing solution
Web load balancing (Load Balancing), simply put, is to allocate "work tasks" to our server cluster, and using appropriate allocation methods is very important for protecting the back-end web servers.
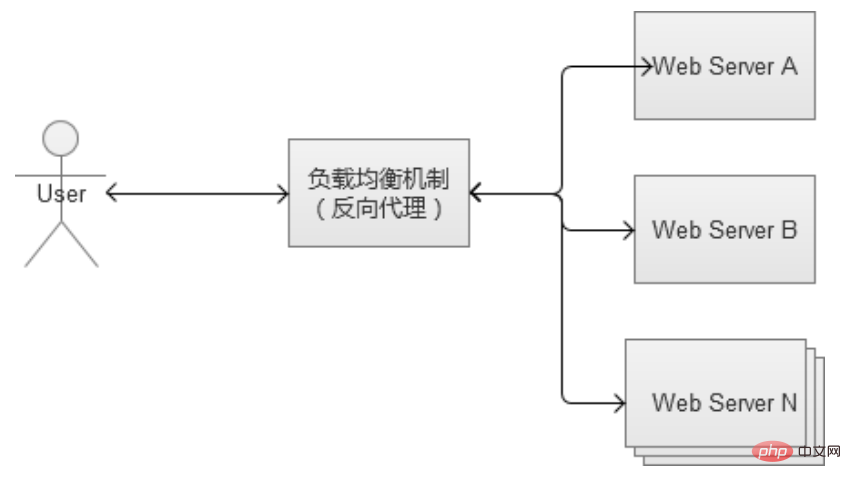
Reverse proxy load balancing
The core work of the reverse proxy service is mainly to forward HTTP requests, playing the role of the browser and the role of backend web server relay. Because it works at the HTTP layer (application layer), which is the seventh layer of the seven-layer network structure, it is also called "seven-layer load balancing". There are many software that can be used as reverse proxy, and one of the more common ones is Nginx.
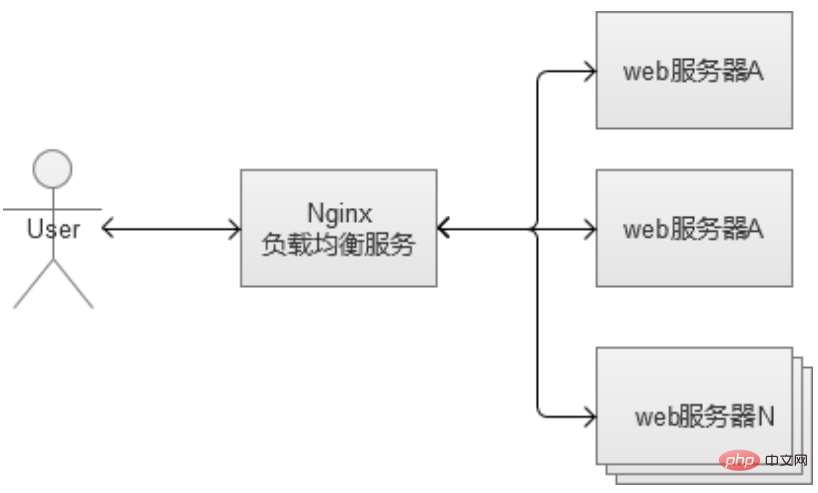
Nginx is a very flexible reverse proxy software that can freely customize forwarding strategies, allocate the weight of server traffic, etc. In reverse proxy, a common problem is the session data stored by the web server, because the general load balancing strategy allocates requests randomly. There is no guarantee that requests from the same logged-in user will be allocated to the same web machine, which will lead to the problem that the session cannot be found.
There are two main solutions:
Configure the forwarding rules of the reverse proxy so that requests from the same user must fall on the same machine (by analyzing cookies ), complex forwarding rules will consume more CPU and increase the burden on the proxy server.
It is recommended to use an independent service to store information such as session, such as redis/memchache.
The reverse proxy service can also enable caching. If enabled, it will increase the burden on the reverse proxy and needs to be used with caution. This load balancing strategy is very simple to implement and deploy, and its performance is relatively good. However, it has the problem of "single point of failure". If it hangs, it will cause a lot of trouble. Moreover, as the number of Web servers continues to increase in the later stages, it itself may become a bottleneck of the system.
Configuration file sample:
#user nobody; worker_processes 1; #pid logs/nginx.pid; events {
worker_connections 1024; } http {
include mime.types;
default_type application/octet-stream;
sendfile on;
keepalive_timeout 65;
upstream www.hcoder.net {
server 192.168.1.188:80 weight=5;
server 192.168.1.158:80;
}
server {
listen 80;
server_name www.hcoder.net;
location / {
proxy_pass http://www.hcoder.net;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
} }The above is the detailed content of Website load balancing solution. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How do I use regular expressions (regex) in Linux for pattern matching?
Mar 17, 2025 pm 05:25 PM
How do I use regular expressions (regex) in Linux for pattern matching?
Mar 17, 2025 pm 05:25 PM
The article explains how to use regular expressions (regex) in Linux for pattern matching, file searching, and text manipulation, detailing syntax, commands, and tools like grep, sed, and awk.
 How do I monitor system performance in Linux using tools like top, htop, and vmstat?
Mar 17, 2025 pm 05:28 PM
How do I monitor system performance in Linux using tools like top, htop, and vmstat?
Mar 17, 2025 pm 05:28 PM
The article discusses using top, htop, and vmstat for monitoring Linux system performance, detailing their unique features and customization options for effective system management.
 How do I implement two-factor authentication (2FA) for SSH in Linux?
Mar 17, 2025 pm 05:31 PM
How do I implement two-factor authentication (2FA) for SSH in Linux?
Mar 17, 2025 pm 05:31 PM
The article provides a guide on setting up two-factor authentication (2FA) for SSH on Linux using Google Authenticator, detailing installation, configuration, and troubleshooting steps. It highlights the security benefits of 2FA, such as enhanced sec
 How do I configure SELinux or AppArmor to enhance security in Linux?
Mar 12, 2025 pm 06:59 PM
How do I configure SELinux or AppArmor to enhance security in Linux?
Mar 12, 2025 pm 06:59 PM
This article compares SELinux and AppArmor, Linux kernel security modules providing mandatory access control. It details their configuration, highlighting the differences in approach (policy-based vs. profile-based) and potential performance impacts
 How do I back up and restore a Linux system?
Mar 12, 2025 pm 07:01 PM
How do I back up and restore a Linux system?
Mar 12, 2025 pm 07:01 PM
This article details Linux system backup and restoration methods. It compares full system image backups with incremental backups, discusses optimal backup strategies (regularity, multiple locations, versioning, testing, security, rotation), and da
 How do I use sudo to grant elevated privileges to users in Linux?
Mar 17, 2025 pm 05:32 PM
How do I use sudo to grant elevated privileges to users in Linux?
Mar 17, 2025 pm 05:32 PM
The article explains how to manage sudo privileges in Linux, including granting, revoking, and best practices for security. Key focus is on editing /etc/sudoers safely and limiting access.Character count: 159
 How do I set up a firewall in Linux using firewalld or iptables?
Mar 12, 2025 pm 06:58 PM
How do I set up a firewall in Linux using firewalld or iptables?
Mar 12, 2025 pm 06:58 PM
This article compares Linux firewall configuration using firewalld and iptables. Firewalld offers a user-friendly interface for managing zones and services, while iptables provides low-level control via command-line manipulation of the netfilter fra
 How do I manage software packages in Linux using package managers (apt, yum, dnf)?
Mar 17, 2025 pm 05:26 PM
How do I manage software packages in Linux using package managers (apt, yum, dnf)?
Mar 17, 2025 pm 05:26 PM
Article discusses managing software packages in Linux using apt, yum, and dnf, covering installation, updates, and removals. It compares their functionalities and suitability for different distributions.






