CI框架源码阅读---------Security.php_PHP教程
defined
dir
php
框架
源码
阅读
[php]
/**
* CodeIgniter
*
* An open source application development framework for PHP 5.1.6 or newer
*
* @package CodeIgniter
* @author ExpressionEngine Dev Team
* @copyright Copyright (c) 2008 - 2011, EllisLab, Inc.
* @license http://codeigniter.com/user_guide/license.html
* @link http://codeigniter.com
* @since Version 1.0
* @filesource
*/
// ------------------------------------------------------------------------
/**
* Security Class
* 本类包含一些方法,能帮助您创建安全的应用程序,对输入的数据进行安全方面的处理。
* CI官方手册本类的地址:http://codeigniter.org.cn/user_guide/libraries/security.html
* @package CodeIgniter
* @subpackage Libraries
* @category Security
* @author ExpressionEngine Dev Team
* @link http://codeigniter.com/user_guide/libraries/security.html
*/
class CI_Security {
/**
* Random Hash for protecting URLs
* 为保护URL(跨站脚本攻击)的随机hash值
* @var string
* @access protected
*/
protected $_xss_hash = '';
/**
* Random Hash for Cross Site Request Forgery Protection Cookie
* 防止跨站请求伪造cookie的随机hash
* @var string
* @access protected
*/
protected $_csrf_hash = '';
/**
* Expiration time for Cross Site Request Forgery Protection Cookie
* Defaults to two hours (in seconds)
* 跨站请求保护Cookie的过期时间,默认是2小时(单位秒)
* @var int
* @access protected
*/
protected $_csrf_expire = 7200;
/**
* Token name for Cross Site Request Forgery 伪造 Protection Cookie
* 跨站请求伪造保护的Cookie令牌名
* @var string
* @access protected
*/
protected $_csrf_token_name = 'ci_csrf_token';
/**
* Cookie name for Cross Site Request Forgery Protection Cookie
* 跨站请求伪造保护的Cookie的Cookie名
* @var string
* @access protected
*/
protected $_csrf_cookie_name = 'ci_csrf_token';
/**
* List of never allowed strings
* 决不允许的字符串的列表
* @var array
* @access protected
*/
protected $_never_allowed_str = array(
'document.cookie' => '[removed]',
'document.write' => '[removed]',
'.parentNode' => '[removed]',
'.innerHTML' => '[removed]',
'window.location' => '[removed]',
'-moz-binding' => '[removed]',
'' => '-->',
' '
'' => ''
);
/* never allowed, regex replacement */
/**
* List of never allowed regex replacement
* 不允许的正则替换字符串列表
* @var array
* @access protected
*/
protected $_never_allowed_regex = array(
'javascript\s*:',
'expression\s*(\(|&\#40;)', // CSS and IE
'vbscript\s*:', // IE, surprise!
'Redirect\s+302',
"([\"'])?data\s*:[^\\1]*?base64[^\\1]*?,[^\\1]*?\\1?"
);
/**
* Constructor
*
* @return void
*/
public function __construct()
{
// Is CSRF protection enabled?
// csrf 是否开启
if (config_item('csrf_protection') === TRUE)
{
// CSRF config 读取CSRF 配置并赋值给本类下的对应的属性
foreach (array('csrf_expire', 'csrf_token_name', 'csrf_cookie_name') as $key)
{
if (FALSE !== ($val = config_item($key)))
{
$this->{'_'.$key} = $val;
}
}
// Append application specific cookie prefix
// 添加应用指定的cookie前缀
if (config_item('cookie_prefix'))
{
$this->_csrf_cookie_name = config_item('cookie_prefix').$this->_csrf_cookie_name;
}
// Set the CSRF hash
// 设置CSRF hash
$this->_csrf_set_hash();
}
log_message('debug', "Security Class Initialized");
}
// --------------------------------------------------------------------
/**
* Verify Cross Site Request Forgery Protection
* 验证跨站请求伪造保护
* @return object
*/
public function csrf_verify()
{
// If it's not a POST request we will set the CSRF cookie
// 如果不是post请求我们要设置 CSRF cookie
if (strtoupper($_SERVER['REQUEST_METHOD']) !== 'POST')
{
return $this->csrf_set_cookie();
}
// Do the tokens exist in both the _POST and _COOKIE arrays?
// 如果请求令牌不存在,调用csrf_show_error 报错
if ( ! isset($_POST[$this->_csrf_token_name], $_COOKIE[$this->_csrf_cookie_name]))
{
$this->csrf_show_error();
}
// Do the tokens match?
// 如果令牌不对,报错。
if ($_POST[$this->_csrf_token_name] != $_COOKIE[$this->_csrf_cookie_name])
{
$this->csrf_show_error();
}
// We kill this since we're done and we don't want to
// polute the _POST array
// 销毁领牌子,因为我们不想污染_POST 数组
unset($_POST[$this->_csrf_token_name]);
// Nothing should last forever
// 销毁cookie名 并重新设置hash和cookie
unset($_COOKIE[$this->_csrf_cookie_name]);
$this->_csrf_set_hash();
$this->csrf_set_cookie();
log_message('debug', 'CSRF token verified');
return $this;
}
// --------------------------------------------------------------------
/**
* Set Cross Site Request Forgery Protection Cookie
* 设置伪造cookie保护跨站请求
* @return object
*/
public function csrf_set_cookie()
{
$expire = time() + $this->_csrf_expire;
$secure_cookie = (config_item('cookie_secure') === TRUE) ? 1 : 0;
// 当存在https时设置cookie
if ($secure_cookie && (emptyempty($_SERVER['HTTPS']) OR strtolower($_SERVER['HTTPS']) === 'off'))
{
return FALSE;
}
// 设置cookie
setcookie($this->_csrf_cookie_name, $this->_csrf_hash, $expire, config_item('cookie_path'), config_item('cookie_domain'), $secure_cookie);
log_message('debug', "CRSF cookie Set");
return $this;
}
// --------------------------------------------------------------------
/**
* Show CSRF Error
* 显示CSRF错误
* @return void
*/
public function csrf_show_error()
{
show_error('The action you have requested is not allowed.');
}
// --------------------------------------------------------------------
/**
* Get CSRF Hash
* 获取CSRF hash
* Getter Method
*
* @return string self::_csrf_hash
*/
public function get_csrf_hash()
{
return $this->_csrf_hash;
}
// --------------------------------------------------------------------
/**
* Get CSRF Token Name
* 获取CSRF 令排名
* Getter Method
*
* @return string self::csrf_token_name
*/
public function get_csrf_token_name()
{
return $this->_csrf_token_name;
}
// --------------------------------------------------------------------
/**
* XSS Clean
*
* Sanitizes 清理 data so that Cross Site Scripting Hacks can be
* prevented.阻止 This function does a fair amount of work but
* it is extremely thorough, designed to prevent even the
* most obscure XSS attempts 企图. Nothing is ever 100% foolproof,
* of course, but I haven't been able to get anything passed
* the filter.
* 对数据进行过滤,从而可以防止跨站脚本攻击。这个函数做了一些工作,但是它是非常彻底的,
* 甚至可以防止大多数模糊的XSS企图。当然,没有什么是100%安全的,
* 但是我们在这个过滤器中已经做了所欲我们所能做想到的了。
*
* Note: This function should only be used to deal with data
* upon submission. It's not something that should
* be used for general runtime processing.
* 注意:这个函数只能用来处理已经提交的数据。
* 在通常的运行过程中,不应该使用该函数。
*
* This function was based in part on some code and ideas I
* got from Bitflux: http://channel.bitflux.ch/wiki/XSS_Prevention
*
* To help develop this script I used this great list of
* vulnerabilities along with a few other hacks I've
* harvested from examining vulnerabilities in other programs:
* http://ha.ckers.org/xss.html
*
* @param mixed string or array
* @param bool
* @return string
*/
public function xss_clean($str, $is_image = FALSE)
{
/*
* Is the string an array?
* 需要过滤的字符串是数组吗?
*
*/
if (is_array($str))
{
while (list($key) = each($str))
{
$str[$key] = $this->xss_clean($str[$key]);
}
return $str;
}
/*
* Remove Invisible Characters
* 移除不可见字符
*/
$str = remove_invisible_characters($str);
// Validate Entities in URLs
// 验证在URL中的字符实体
$str = $this->_validate_entities($str);
/*
* URL Decode
* URL解码
* Just in case stuff like this is submitted:
* 防止下面这样的东西提交
* Google
*
* Note: Use rawurldecode() so it does not remove plus signs
* rawurldecode() 不会把加号('+')解码为空格,而 urldecode() 可以。
*
*/
$str = rawurldecode($str);
/*
* Convert character entities to ASCII
* 把实体字符转换成ASCII码
* 这使得我们下面的测试是可靠的,我们仅仅转换实体内的标签,因为这些是会造成安全问题的实体
* This permits our tests below to work reliably.
* We only convert entities that are within tags since
* these are the ones that will pose security problems.
*
*/
$str = preg_replace_callback("/[a-z]+=([\'\"]).*?\\1/si", array($this, '_convert_attribute'), $str);
$str = preg_replace_callback("/|
/*
* Remove Invisible Characters Again!
* 再次删除不可见字符
*/
$str = remove_invisible_characters($str);
/*
* Convert all tabs to spaces
* 转换所有制表符为空格
* This prevents strings like this: ja vascript
* 这用来防止字符串类似于ja vascript
* NOTE: we deal with spaces between characters later.
* 注意: 我们将在后面处理字符之间的空格
* NOTE: preg_replace was found to be amazingly slow here on
* large blocks of data, so we use str_replace.
* 注意:preg_replace在这里是极其缓慢的对于大块的数据,所以使用str_replace
*
*/
if (strpos($str, "\t") !== FALSE)
{
$str = str_replace("\t", ' ', $str);
}
/*
* Capture 捕获 converted string for later comparison
* 为以后的比较捕获转换的字符串
*/
$converted_string = $str;
// Remove Strings that are never allowed
// 删除绝不容许的字符串
$str = $this->_do_never_allowed($str);
/*
* Makes PHP tags safe
* 使PHP标签安全
* Note: XML tags are inadvertently replaced too:
* 注意: XML标签也会被无意的替换
*
*
* But it doesn't seem to pose a problem.
* 但是它似乎不会构成问题
*/
if ($is_image === TRUE)
{
// Images have a tendency to have the PHP short opening and
// closing tags every so often so we skip those and only
// do the long opening tags.
$str = preg_replace('/
}
else
{
$str = str_replace(array('', '?'.'>'), array('', '?>'), $str);
}
/*
* Compact any exploded words
* 压缩所有分解了的单词
* This corrects words like: j a v a s c r i p t
* These words are compacted back to their correct state.
*/
$words = array(
'javascript', 'expression', 'vbscript', 'script', 'base64',
'applet', 'alert', 'document', 'write', 'cookie', 'window'
);
foreach ($words as $word)
{
$temp = '';
for ($i = 0, $wordlen = strlen($word); $i
{
$temp .= substr($word, $i, 1)."\s*";
}
// We only want to do this when it is followed by a non-word character
// That way valid stuff like "dealer to" does not become "dealerto"
$str = preg_replace_callback('#('.substr($temp, 0, -3).')(\W)#is', array($this, '_compact_exploded_words'), $str);
}
/*
* Remove disallowed Javascript in links or img tags
* 移除在链接和图片标签中不允许的javascript代码
* We used to do some version comparisons and use of stripos for PHP5,
* 我们通常在PHP5中使用stripos做一些版本的比较,
* but it is dog slow compared to these simplified non-capturing
* 但是特别是当模式在字符串中存在的时候,它要比非捕获的preg_match()慢很多
* preg_match(), especially if the pattern exists in the string
*/
do
{
$original = $str;
if (preg_match("/
{
$str = preg_replace_callback("#]*?)(>|$)#si", array($this, '_js_link_removal'), $str);
}
if (preg_match("/![CI框架源码阅读---------Security.php_PHP教程]()
{
$str = preg_replace_callback("#![CI框架源码阅读---------Security.php_PHP教程]() ]*?)(\s?/?>|$)#si", array($this, '_js_img_removal'), $str);
]*?)(\s?/?>|$)#si", array($this, '_js_img_removal'), $str);
}
if (preg_match("/script/i", $str) OR preg_match("/xss/i", $str))
{
$str = preg_replace("##si", '[removed]', $str);
}
}
while($original != $str);
unset($original);
// Remove evil attributes such as style, onclick and xmlns
// 移除有害的属性,比如style , onclick , xmlns
$str = $this->_remove_evil_attributes($str, $is_image);
/*
* Sanitize naughty HTML elements
* 清理不适当的HTML元素
* If a tag containing any of the words in the list
* below is found, the tag gets converted to entities.
* 如果一个标签包含任何一个下面列表中的单词,这个标签转换为一个字符实体
* So this:
* Becomes:
*/
$naughty = 'alert|applet|audio|basefont|base|behavior|bgsound|blink|body|embed|expression|form|frameset|frame|head|html|ilayer|iframe|input|isindex|layer|link|meta|object|plaintext|style|script|textarea|title|video|xml|xss';
$str = preg_replace_callback('#
/*
* Sanitize naughty scripting elements
* 清理不合法的脚本元素
* Similar to above, only instead of looking for
* tags it looks for PHP and JavaScript commands
* that are disallowed. Rather than removing the
* code, it simply converts the parenthesis to entities
* rendering the code un-executable.
* 上面的类似,仅仅替换查询到的类似于PHP和Javascript命令的不被允许的标签
* 胜过移除这些代码,转换这些代码为不可执行的实体更好
*
* For example: eval('some code')
* Becomes: eval('some code')
*/
$str = preg_replace('#(alert|cmd|passthru|eval|exec|expression|system|fopen|fsockopen|file|file_get_contents|readfile|unlink)(\s*)\((.*?)\)#si', "\\1\\2(\\3)", $str);
// Final clean up
// 最后的清理
// This adds a bit of extra precaution in case
// something got through the above filters
// 额外预防,防止上面的处理产生不合法的字符
$str = $this->_do_never_allowed($str);
/*
* Images are Handled in a Special Way
* - Essentially, we want to know that after all of the character
* conversion is done whether any unwanted, likely XSS, code was found.
* If not, we return TRUE, as the image is clean.
* However, if the string post-conversion does not matched the
* string post-removal of XSS, then it fails, as there was unwanted XSS
* code found and removed/changed during processing.
*/
if ($is_image === TRUE)
{
return ($str == $converted_string) ? TRUE: FALSE;
}
log_message('debug', "XSS Filtering completed");
return $str;
}
// --------------------------------------------------------------------
/**
* Random Hash for protecting URLs
* 随即生成一个_xss_hssh
* @return string
*/
public function xss_hash()
{
if ($this->_xss_hash == '')
{
mt_srand();
$this->_xss_hash = md5(time() + mt_rand(0, 1999999999));
}
return $this->_xss_hash;
}
// --------------------------------------------------------------------
/**
* HTML Entities Decode
* HTML 实体解码
* This function is a replacement for html_entity_decode()
* 这个函数用来替换 html_entity_decode()函数
* The reason we are not using html_entity_decode() by itself is because
* while it is not technically技术上 correct to leave out the semicolon
* at the end of an entity most browsers will still interpret the entity
* correctly. html_entity_decode() does not convert entities without
* semicolons, so we are left with our own little solution here. Bummer.
* 当编码字符后没有写;时,大部分浏览器都能够正确的解释代码,但是,html_entity_decode将不会解释它
* html_entity_decode()不会转换没有分号的实体,所以使用自己的解决方案
* @param string
* @param string
* @return string
*/
public function entity_decode($str, $charset='UTF-8')
{
if (stristr($str, '&') === FALSE)
{
return $str;
}
$str = html_entity_decode($str, ENT_COMPAT, $charset);
$str = preg_replace('~(0*[0-9a-f]{2,5})~ei', 'chr(hexdec("\\1"))', $str);
return preg_replace('~([0-9]{2,4})~e', 'chr(\\1)', $str);
}
// --------------------------------------------------------------------
/**
* Filename Security
* 文件名安全
* @param string
* @param bool
* @return string
*/
public function sanitize_filename($str, $relative_path = FALSE)
{
$bad = array(
"../",
"",
"
">",
"'",
'"',
'&',
'$',
'#',
'{',
'}',
'[',
']',
'=',
';',
'?',
"%20",
"%22",
"%3c", //
"%253c", //
"%3e", // >
"%0e", // >
"%28", // (
"%29", // )
"%2528", // (
"%26", // &
"%24", // $
"%3f", // ?
"%3b", // ;
"%3d" // =
);
if ( ! $relative_path)
{
$bad[] = './';
$bad[] = '/';
}
$str = remove_invisible_characters($str, FALSE);
return stripslashes(str_replace($bad, '', $str));
}
// ----------------------------------------------------------------
/**
* Compact Exploded Words
* 压缩搜索到得单词
* Callback function for xss_clean() to remove whitespace from
* things like j a v a s c r i p t
* 回调函数,用于xss_clean(),从类似于 j a v a s c r i p t中移除空格
*
*
* @param type
* @return type
*/
protected function _compact_exploded_words($matches)
{
return preg_replace('/\s+/s', '', $matches[1]).$matches[2];
}
// --------------------------------------------------------------------
/*
* Remove Evil HTML Attributes (like evenhandlers and style)
* 移除有害的html属性,(像事件处理和样式)
* It removes the evil attribute and either:
* - Everything up until a space
* For example, everything between the pipes:
* - Everything inside the quotes
* For example, everything between the pipes:
*
* @param string $str The string to check
* @param boolean $is_image TRUE if this is an image
* @return string The string with the evil attributes removed
*/
protected function _remove_evil_attributes($str, $is_image)
{
// All javascript event handlers (e.g. onload, onclick, onmouseover), style, and xmlns
// 所有的havascript事件处理器
$evil_attributes = array('on\w*', 'style', 'xmlns', 'formaction');
if ($is_image === TRUE)
{
/*
* Adobe Photoshop puts XML metadata into JFIF images,
* including namespacing, so we have to allow this for images.
* Adobe Photoshop在JFIF图片中放入了XML元数据
* 包含命名空间,所以我们必须对图片允许这些
*/
unset($evil_attributes[array_search('xmlns', $evil_attributes)]);
}
do {
$count = 0;
$attribs = array();
// find occurrences of illegal attribute strings without quotes
// 找出没有加引号的的不合法的属性
preg_match_all('/('.implode('|', $evil_attributes).')\s*=\s*([^\s>]*)/is', $str, $matches, PREG_SET_ORDER);
foreach ($matches as $attr)
{
$attribs[] = preg_quote($attr[0], '/');
}
// find occurrences of illegal 非法 attribute strings with quotes (042 and 047 are octal quotes)
// 找出没有引号的不合法属性(042,4,0是八进制引号)
preg_match_all("/(".implode('|', $evil_attributes).")\s*=\s*(\042|\047)([^\\2]*?)(\\2)/is", $str, $matches, PREG_SET_ORDER);
foreach ($matches as $attr)
{
$attribs[] = preg_quote($attr[0], '/');
}
// replace illegal attribute strings that are inside an html tag
// 替换html标签中的非法属性
if (count($attribs) > 0)
{
$str = preg_replace("/\-])(.*?)(".implode('|', $attribs).")(.*?)([\s>
}
} while ($count);
return $str;
}
// --------------------------------------------------------------------
/**
* Sanitize Naughty HTML
* 消除有害的html
* Callback function for xss_clean() to remove naughty HTML elements
*
* @param array
* @return string
*/
protected function _sanitize_naughty_html($matches)
{
// encode opening brace
$str = '
// encode captured opening or closing brace to prevent recursive vectors
$str .= str_replace(array('>', '', '
$matches[4]);
return $str;
}
// --------------------------------------------------------------------
/**
* JS Link Removal
* js链接清理
* Callback function for xss_clean() to sanitize links
* This limits the PCRE backtracks, making it more performance friendly
* and prevents PREG_BACKTRACK_LIMIT_ERROR from being triggered in
* PHP 5.2+ on link-heavy strings
* 调用xss_clean 清理连接
* @param array
* @return string
*/
protected function _js_link_removal($match)
{
return str_replace(
$match[1],
preg_replace(
'#href=.*?(alert\(|alert&\#40;|javascript\:|livescript\:|mocha\:|charset\=|window\.|document\.|\.cookie|<script>
<div> '', </script>
$this->_filter_attributes(str_replace(array(''), '', $match[1]))
),
$match[0]
);
}
// --------------------------------------------------------------------
/**
* JS Image Removal
* js图片清理
* Callback function for xss_clean() to sanitize image tags
* This limits the PCRE backtracks, making it more performance friendly
* and prevents PREG_BACKTRACK_LIMIT_ERROR from being triggered in
* PHP 5.2+ on image tag heavy strings
*
* @param array
* @return string
*/
protected function _js_img_removal($match)
{
return str_replace(
$match[1],
preg_replace(
'#src=.*?(alert\(|alert&\#40;|javascript\:|livescript\:|mocha\:|charset\=|window\.|document\.|\.cookie|<script>
<div> '', </script>
$this->_filter_attributes(str_replace(array(''), '', $match[1]))
),
$match[0]
);
}
// --------------------------------------------------------------------
/**
* Attribute Conversion
* 属性转换
* Used as a callback for XSS Clean
*
* @param array
* @return string
*/
protected function _convert_attribute($match)
{
return str_replace(array('>', '', '
}
// --------------------------------------------------------------------
/**
* Filter Attributes
* 过滤属性
* Filters tag attributes for consistency and safety
* 为一致性和安全性过滤标签属性
* @param string
* @return string
*/
protected function _filter_attributes($str)
{
$out = '';
if (preg_match_all('#\s*[a-z\-]+\s*=\s*(\042|\047)([^\\1]*?)\\1#is', $str, $matches))
{
foreach ($matches[0] as $match)
{
$out .= preg_replace("#/\*.*?\*/#s", '', $match);
}
}
return $out;
}
// --------------------------------------------------------------------
/**
* HTML Entity Decode Callback
* html实体解码
* Used as a callback for XSS Clean
*
* @param array
* @return string
*/
protected function _decode_entity($match)
{
return $this->entity_decode($match[0], strtoupper(config_item('charset')));
}
// --------------------------------------------------------------------
/**
* Validate URL entities
* 验证URL字符实体
* Called by xss_clean()
*
* @param string
* @return string
*/
protected function _validate_entities($str)
{
/*
* Protect GET variables in URLs
* 保护url中的GET变量
*/
// 901119URL5918AMP18930PROTECT8198
$str = preg_replace('|\&([a-z\_0-9\-]+)\=([a-z\_0-9\-]+)|i', $this->xss_hash()."\\1=\\2", $str);
/*
* Validate standard character entities
* 验证标准字符实体
*
* Add a semicolon if missing. We do this to enable
* the conversion of entities to ASCII later.
* 如果没有的话,添加一个分号。这样做是为了以后允许字符实体到ASCII的转换
*
*/
$str = preg_replace('#(&\#?[0-9a-z]{2,})([\x00-\x20])*;?#i', "\\1;\\2", $str);
/*
* Validate UTF16 two byte encoding (x00)
* 验证UTF16两个字节的编码(x00)
* Just as above, adds a semicolon if missing.
* 像上面一样如果不存在添加一个分号。
*/
$str = preg_replace('#(&\#x?)([0-9A-F]+);?#i',"\\1\\2;",$str);
/*
* Un-Protect GET variables in URLs
* URL中不保护的GET变量
*/
$str = str_replace($this->xss_hash(), '&', $str);
return $str;
}
// ----------------------------------------------------------------------
/**
* Do Never Allowed
* 移除不允许的字符
* A utility function for xss_clean()
*
* @param string
* @return string
*/
protected function _do_never_allowed($str)
{
$str = str_replace(array_keys($this->_never_allowed_str), $this->_never_allowed_str, $str);
foreach ($this->_never_allowed_regex as $regex)
{
$str = preg_replace('#'.$regex.'#is', '[removed]', $str);
}
return $str;
}
// --------------------------------------------------------------------
/**
* Set Cross Site Request Forgery Protection Cookie
* 设置跨站请求保护Cookie
* @return string
*/
protected function _csrf_set_hash()
{
if
本站声明
本文内容由网友自发贡献,版权归原作者所有,本站不承担相应法律责任。如您发现有涉嫌抄袭侵权的内容,请联系admin@php.cn

热AI工具

Undresser.AI Undress
人工智能驱动的应用程序,用于创建逼真的裸体照片

AI Clothes Remover
用于从照片中去除衣服的在线人工智能工具。

Undress AI Tool
免费脱衣服图片

Clothoff.io
AI脱衣机

AI Hentai Generator
免费生成ai无尽的。

热门文章
R.E.P.O.能量晶体解释及其做什么(黄色晶体)
3 周前
By 尊渡假赌尊渡假赌尊渡假赌
R.E.P.O.最佳图形设置
3 周前
By 尊渡假赌尊渡假赌尊渡假赌
刺客信条阴影:贝壳谜语解决方案
2 周前
By DDD
R.E.P.O.如果您听不到任何人,如何修复音频
3 周前
By 尊渡假赌尊渡假赌尊渡假赌
WWE 2K25:如何解锁Myrise中的所有内容
4 周前
By 尊渡假赌尊渡假赌尊渡假赌

热工具

记事本++7.3.1
好用且免费的代码编辑器

SublimeText3汉化版
中文版,非常好用

禅工作室 13.0.1
功能强大的PHP集成开发环境

Dreamweaver CS6
视觉化网页开发工具

SublimeText3 Mac版
神级代码编辑软件(SublimeText3)

热门话题
 适用于 Ubuntu 和 Debian 的 PHP 8.4 安装和升级指南
Dec 24, 2024 pm 04:42 PM
适用于 Ubuntu 和 Debian 的 PHP 8.4 安装和升级指南
Dec 24, 2024 pm 04:42 PM
PHP 8.4 带来了多项新功能、安全性改进和性能改进,同时弃用和删除了大量功能。 本指南介绍了如何在 Ubuntu、Debian 或其衍生版本上安装 PHP 8.4 或升级到 PHP 8.4
 讨论 CakePHP
Sep 10, 2024 pm 05:28 PM
讨论 CakePHP
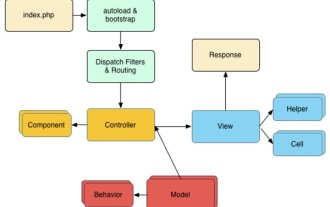
Sep 10, 2024 pm 05:28 PM
CakePHP 是 PHP 的开源框架。它的目的是使应用程序的开发、部署和维护变得更加容易。 CakePHP 基于类似 MVC 的架构,功能强大且易于掌握。模型、视图和控制器 gu
 如何设置 Visual Studio Code (VS Code) 进行 PHP 开发
Dec 20, 2024 am 11:31 AM
如何设置 Visual Studio Code (VS Code) 进行 PHP 开发
Dec 20, 2024 am 11:31 AM
Visual Studio Code,也称为 VS Code,是一个免费的源代码编辑器 - 或集成开发环境 (IDE) - 可用于所有主要操作系统。 VS Code 拥有针对多种编程语言的大量扩展,可以轻松编写
 CakePHP 快速指南
Sep 10, 2024 pm 05:27 PM
CakePHP 快速指南
Sep 10, 2024 pm 05:27 PM
CakePHP 是一个开源MVC 框架。它使开发、部署和维护应用程序变得更加容易。 CakePHP 有许多库可以减少大多数常见任务的过载。
 您如何在PHP中解析和处理HTML/XML?
Feb 07, 2025 am 11:57 AM
您如何在PHP中解析和处理HTML/XML?
Feb 07, 2025 am 11:57 AM
本教程演示了如何使用PHP有效地处理XML文档。 XML(可扩展的标记语言)是一种用于人类可读性和机器解析的多功能文本标记语言。它通常用于数据存储









